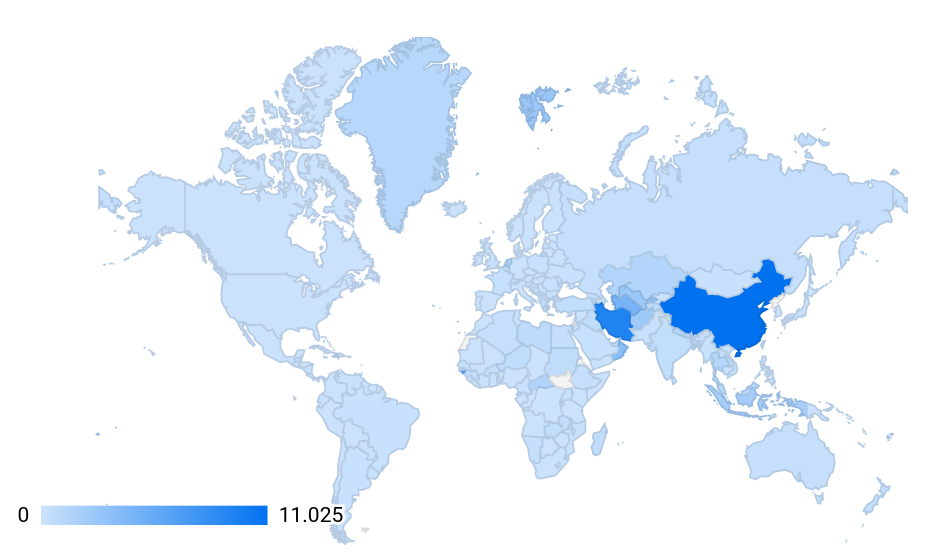
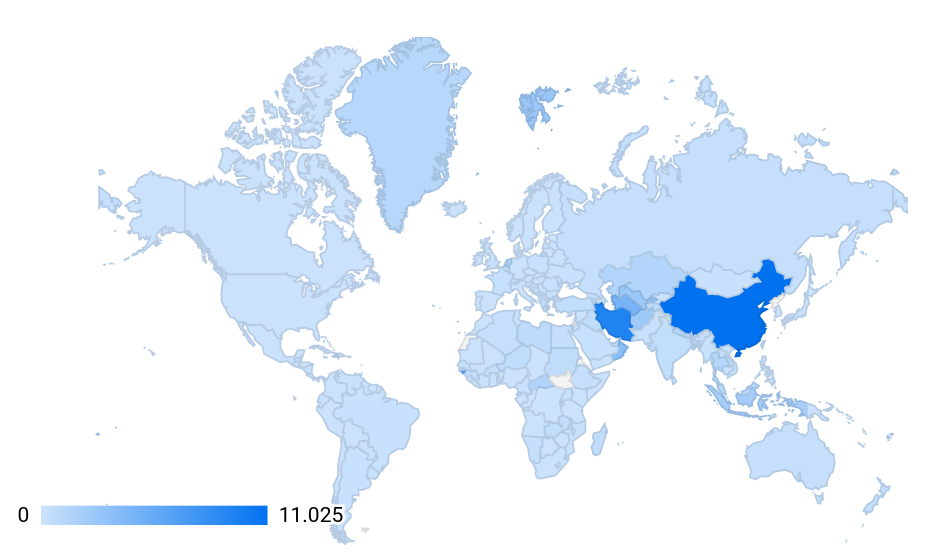
Lack of transparency in censorship and human rights violations by companies such as Google, which by default and without prior notice, it prevents many users from US-sanctioned countries from accessing many sites and services, including non-financial sites, human rights organizations, and security tools, makes conditions for protesting, analyzing and reporting human rights issues very difficult and sometimes impossible in a country like Iran, which, on a par with China, denies people access to many Internet sites and services:
(Is this other than an irony of human rights?)
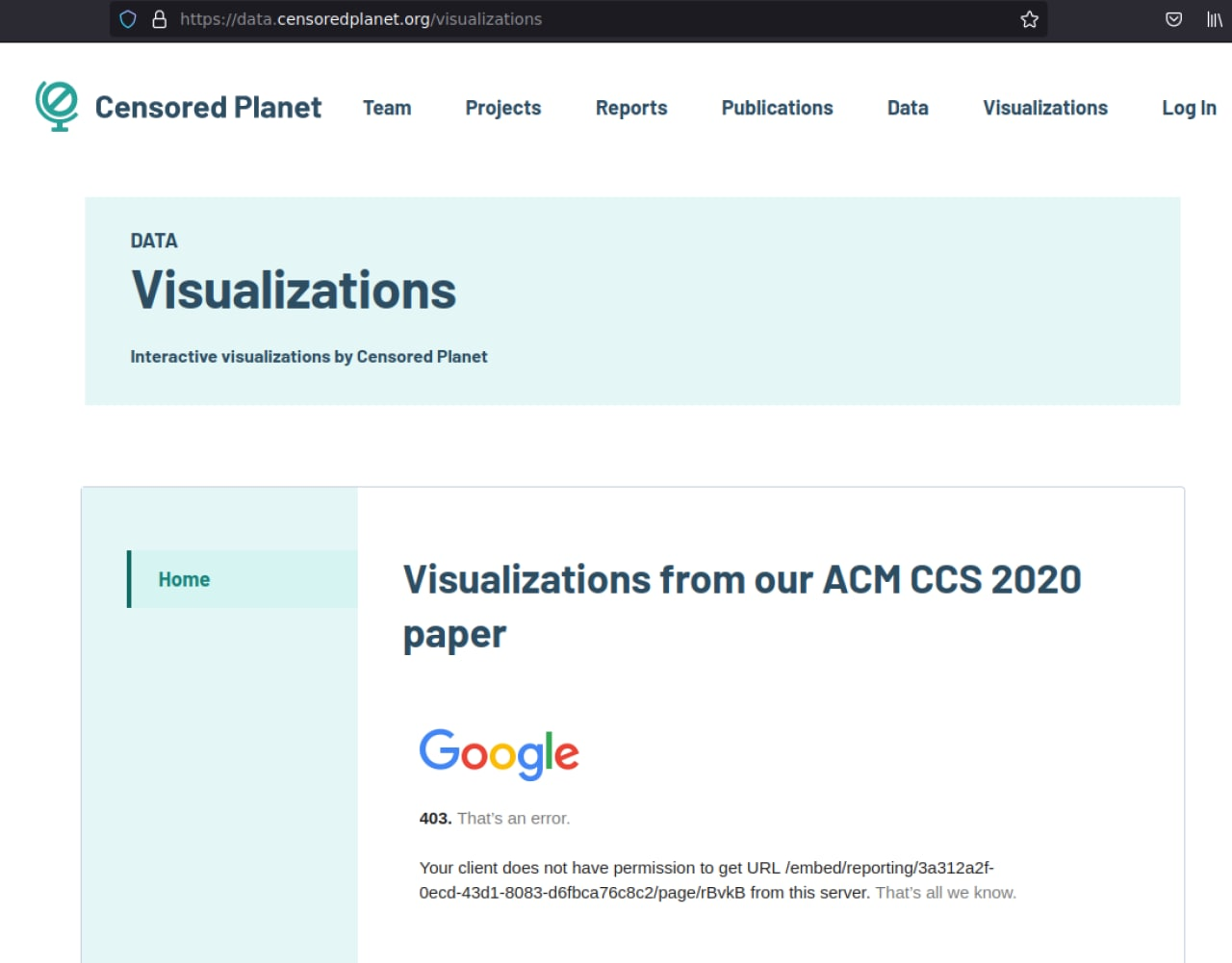
The most common type of blocking users' access due to their IP geolocation is HTTP 403 error. But this error may be caused by the server for any reason, but it is also irrelevant to the embargo. In Google services, differences may be detected through Tor. In the following case, the upper case received a HTTP 403 error as a result of a boycott by Google, and the lower case same error due to an internal server issue:
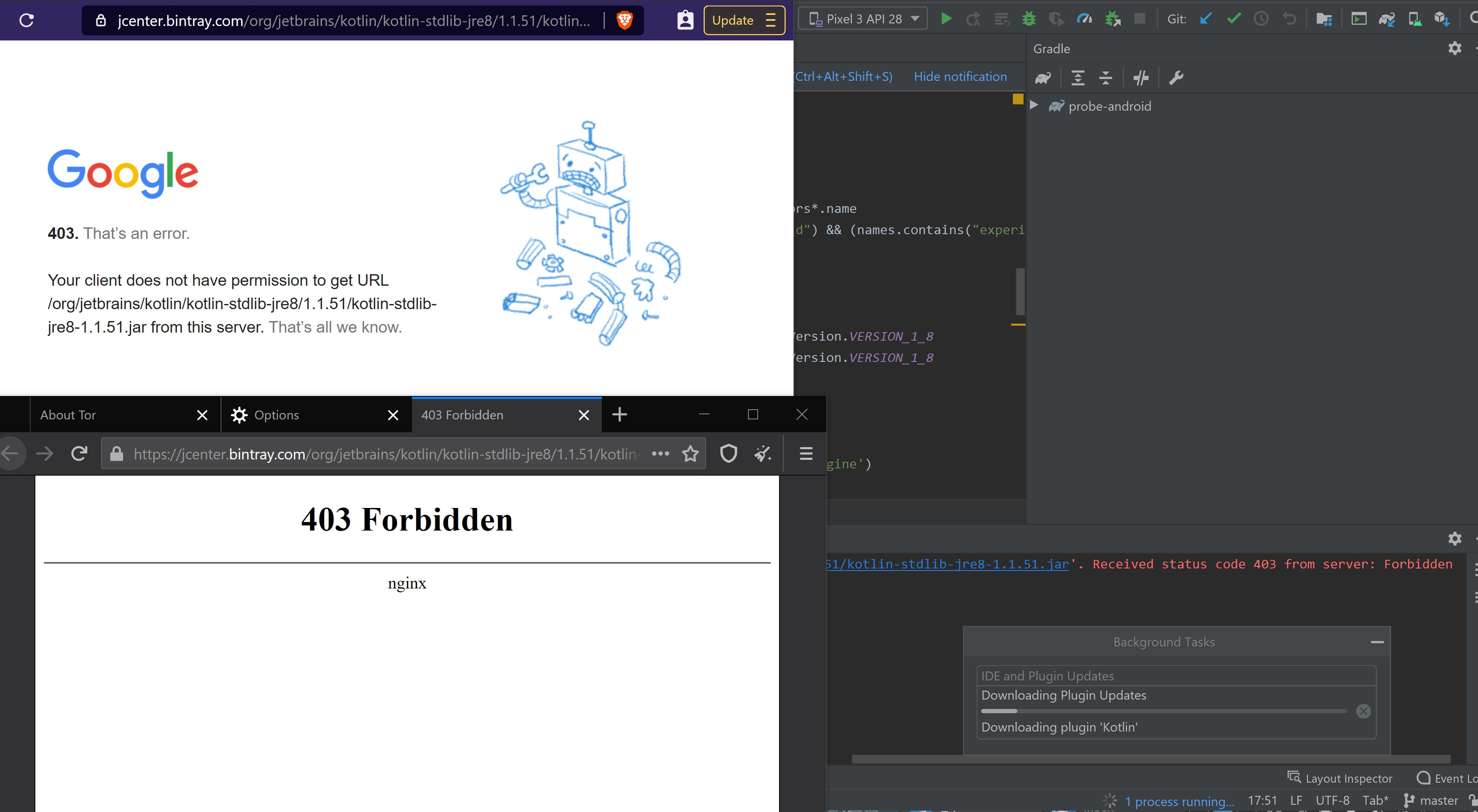
But it still looks different on different servers:

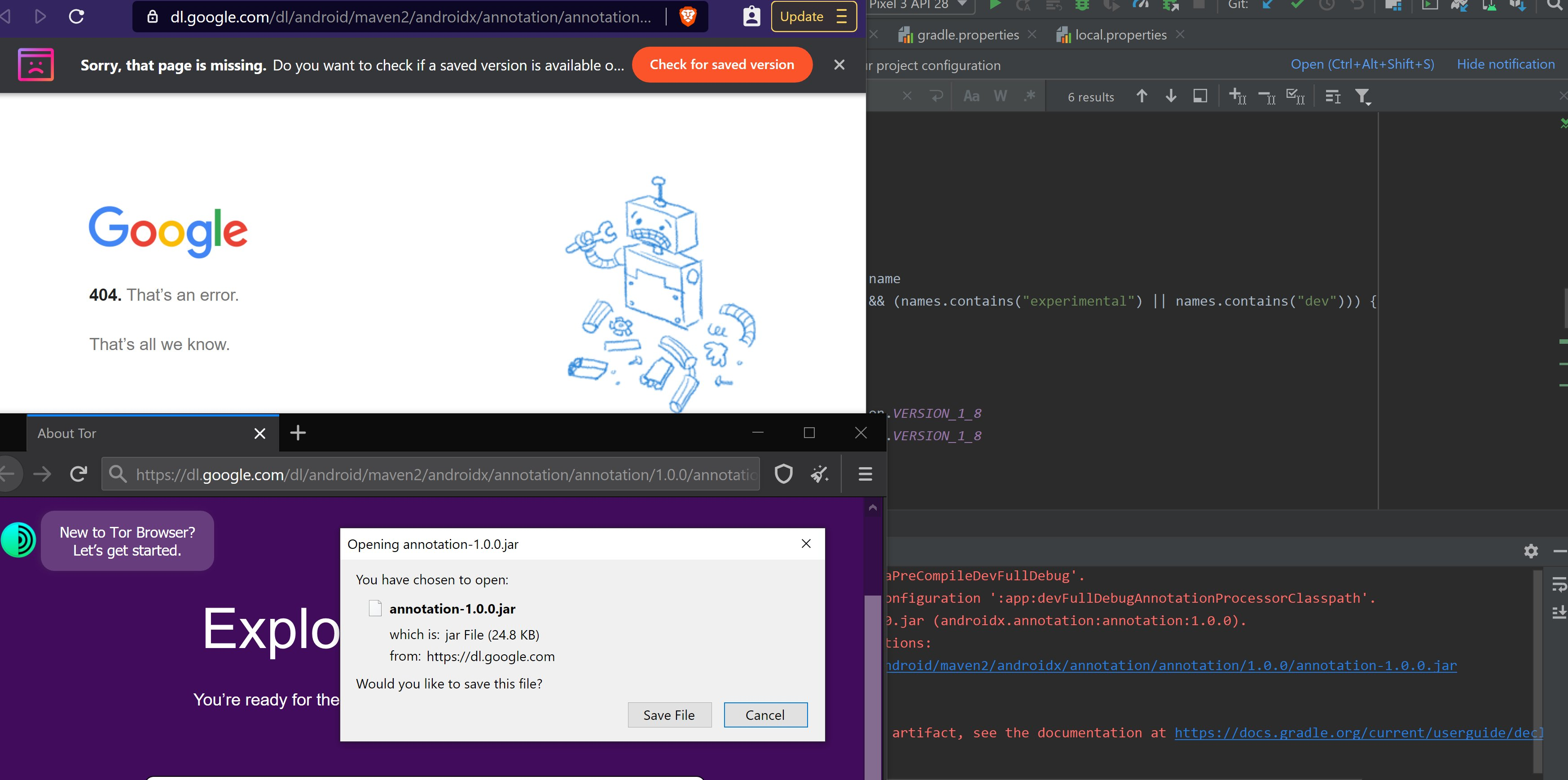
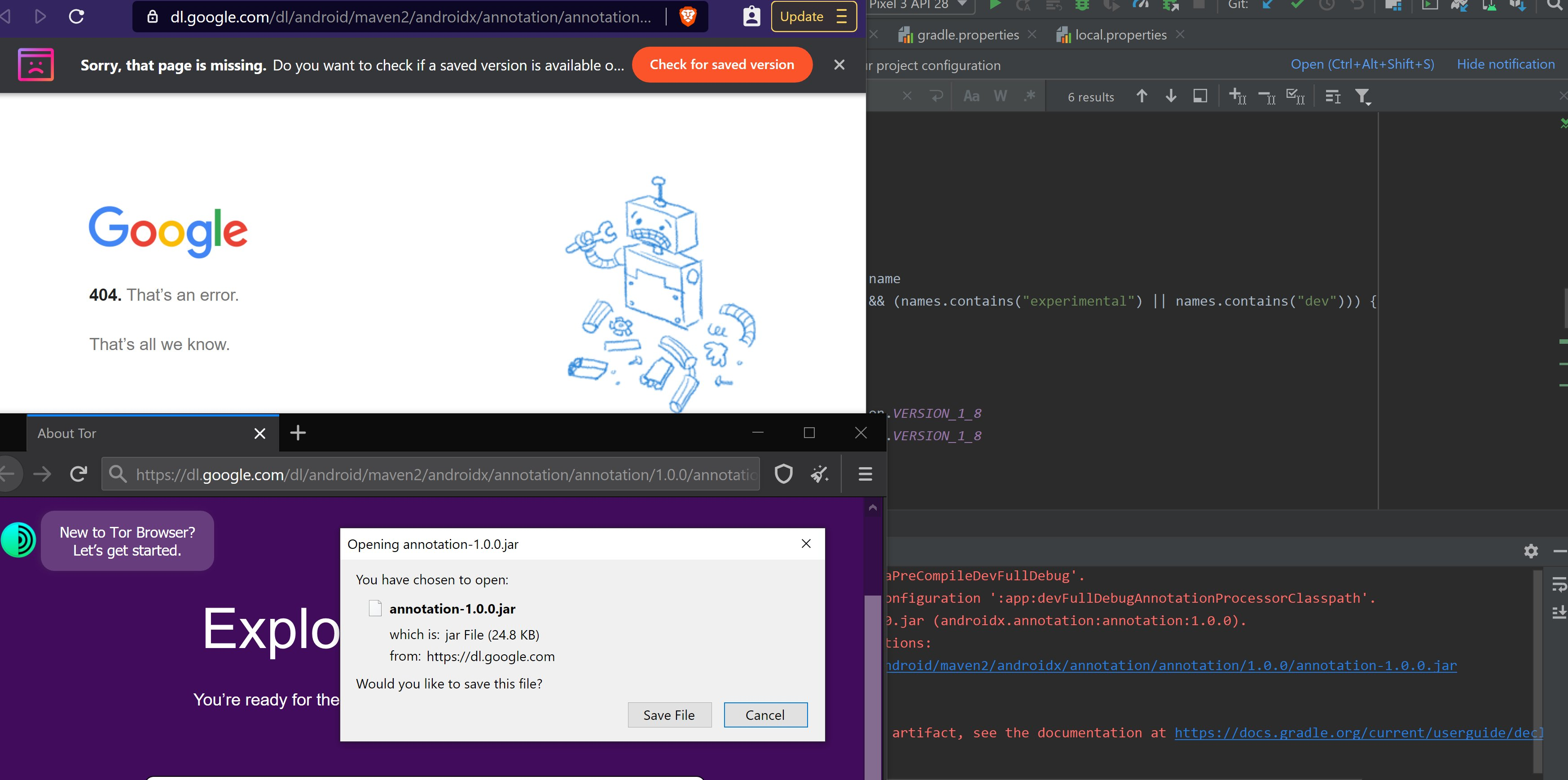
In the following, users see that the boycott by Google is not only with HTTP 403 error, and in some cases users may receive HTTP 404 error:
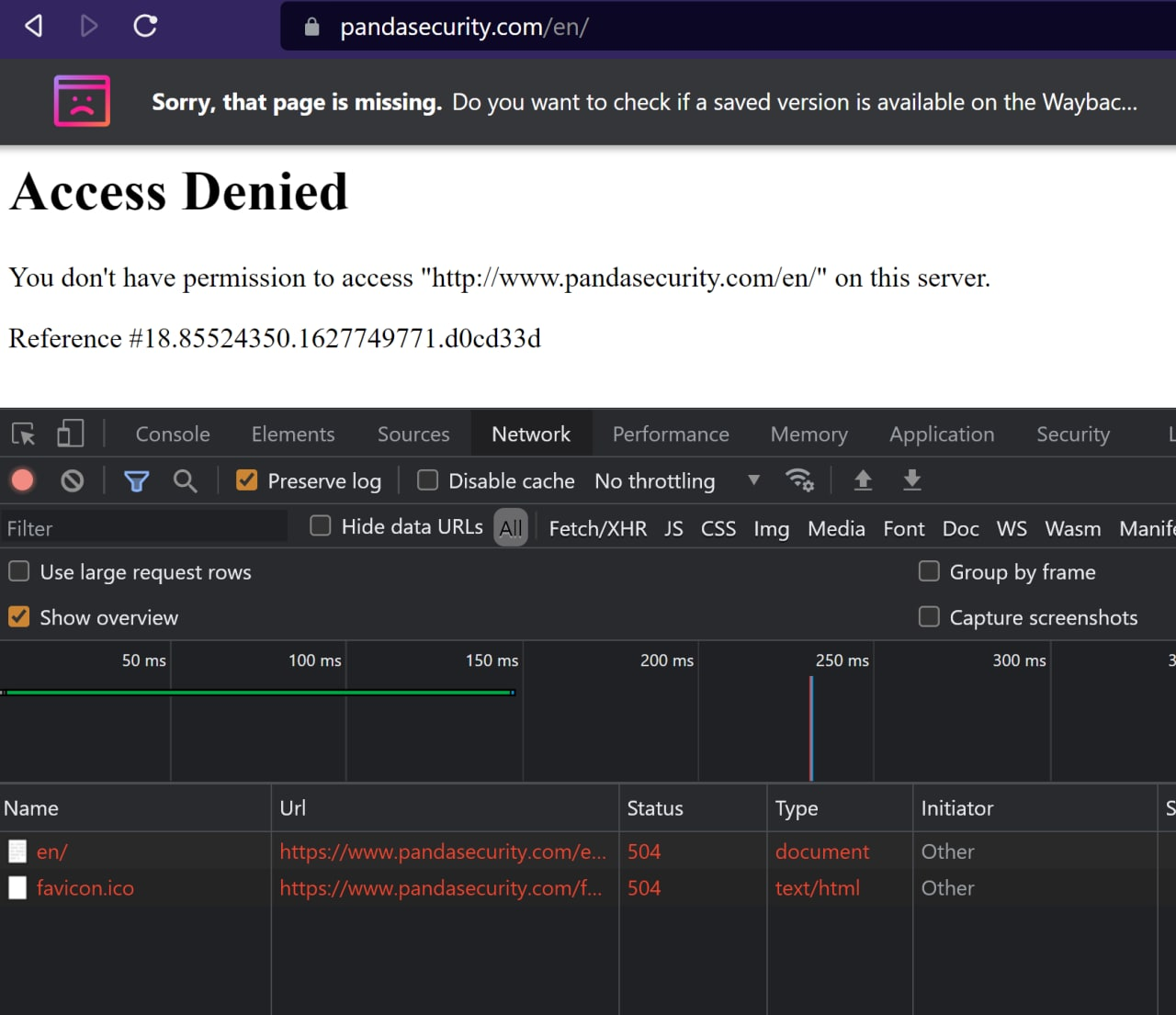
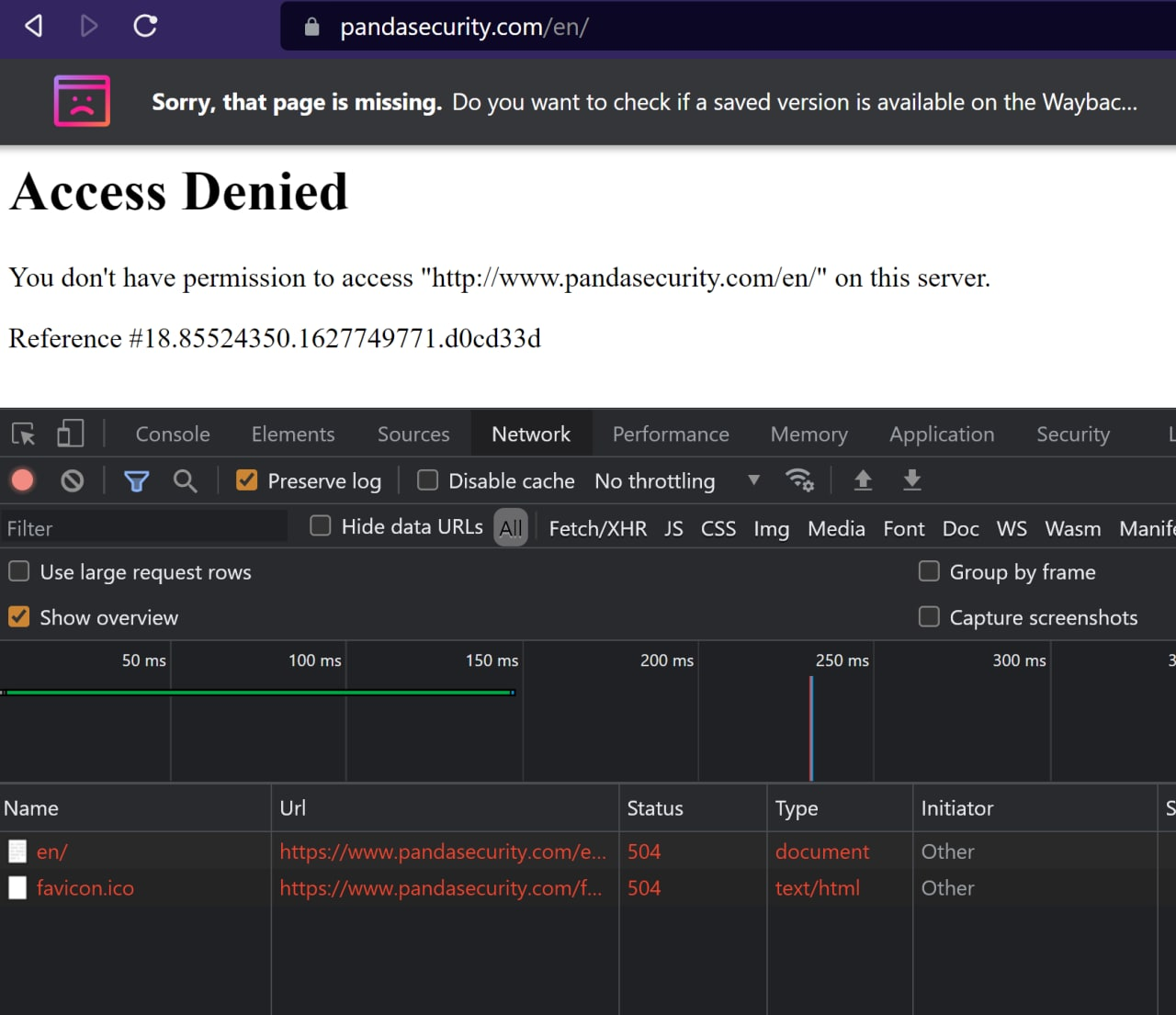
Or in some services, users get HTTP 504 error instead of HTTP 403:
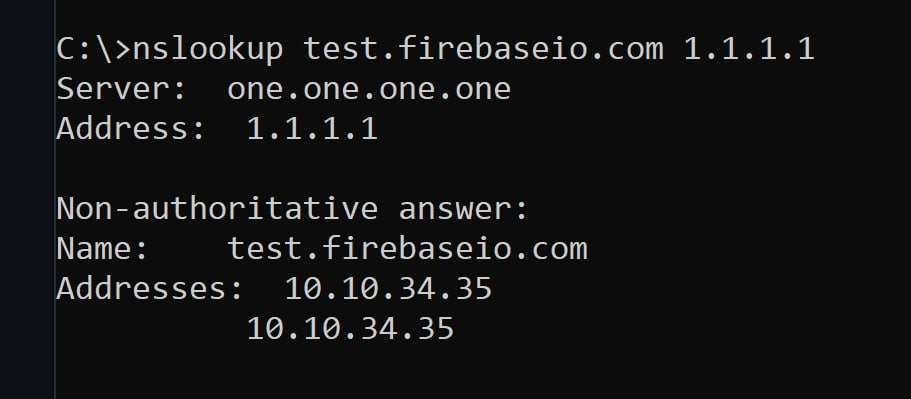
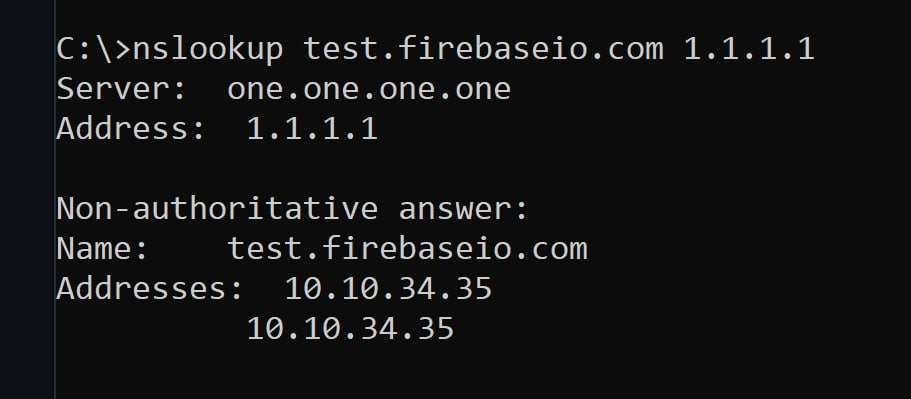
Distinguishing censorship due to sanctions and censorship due to prohibition in the user network is very easy in a successful HTTPS communication. But Google has different ways of boycotting users. Such as blocking TLS communication by the server (after TCP handshake):
From a server in Germany that is now geolocated by Google as Iran:
# curl -v https://test.firebaseio.com/
* Trying 35.201.97.85:443...
* Connected to test.firebaseio.com (35.201.97.85) port 443 (#0)
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: /etc/pki/tls/certs/ca-bundle.crt
* CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* OpenSSL SSL_connect: SSL_ERROR_SYSCALL in connection to test.firebaseio.com:443
* Closing connection 0
curl: (35) OpenSSL SSL_connect: SSL_ERROR_SYSCALL in connection to test.firebaseio.com:443
Use Firebase IP but use example.com for SNI:
# curl -v --resolve 'example.com:443:35.201.97.85' https://example.com/
* Added example.com:443:35.201.97.85 to DNS cache
* Hostname example.com was found in DNS cache
* Trying 35.201.97.85:443...
* Connected to example.com (35.201.97.85) port 443 (#0)
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: /etc/pki/tls/certs/ca-bundle.crt
* CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* OpenSSL SSL_connect: SSL_ERROR_SYSCALL in connection to example.com:443
* Closing connection 0
curl: (35) OpenSSL SSL_connect: SSL_ERROR_SYSCALL in connection to example.com:443
Use tor proxy:
# torsocks curl -v https://test.firebaseio.com/
* Trying 35.201.97.85:443...
* Connected to test.firebaseio.com (35.201.97.85) port 443 (#0)
* ALPN, offering h2
* ALPN, offering http/1.1
* successfully set certificate verify locations:
* CAfile: /etc/pki/tls/certs/ca-bundle.crt
* CApath: none
* TLSv1.3 (OUT), TLS handshake, Client hello (1):
* TLSv1.3 (IN), TLS handshake, Server hello (2):
* TLSv1.2 (IN), TLS handshake, Certificate (11):
* TLSv1.2 (IN), TLS handshake, Server key exchange (12):
* TLSv1.2 (IN), TLS handshake, Server finished (14):
* TLSv1.2 (OUT), TLS handshake, Client key exchange (16):
* TLSv1.2 (OUT), TLS change cipher, Change cipher spec (1):
* TLSv1.2 (OUT), TLS handshake, Finished (20):
* TLSv1.2 (IN), TLS handshake, Finished (20):
* SSL connection using TLSv1.2 / ECDHE-RSA-CHACHA20-POLY1305
* ALPN, server accepted to use http/1.1
* Server certificate:
* subject: CN=firebaseio.com
* start date: Jul 1 20:16:52 2021 GMT
* expire date: Sep 29 20:16:51 2021 GMT
* subjectAltName: host "test.firebaseio.com" matched cert's "*.firebaseio.com"
* issuer: C=US; O=Google Trust Services LLC; CN=GTS CA 1D4
* SSL certificate verify ok.
> GET / HTTP/1.1
> Host: test.firebaseio.com
> User-Agent: curl/7.76.1
> Accept: */*
>
* Mark bundle as not supporting multiuse
< HTTP/1.1 404 Not Found
< Server: nginx
< Date: Sat, 18 Sep 2021 11:05:02 GMT
< Content-Type: text/plain
< Content-Length: 82
< Connection: keep-alive
< Access-Control-Allow-Origin: *
< Strict-Transport-Security: max-age=31556926; includeSubDomains; preload
<
* Connection #0 to host test.firebaseio.com left intact
Firebase error. Please ensure that you spelled the name of your Firebase correctly
Or like blocking TCP communication to some servers:
# traceroute -n ooni.org --tcp -m50 -O info --port=443 -A
traceroute to ooni.org (104.198.14.52), 50 hops max, 60 byte packets
1 192.168.128.1 [*] 192.811 ms 205.170 ms 203.302 ms
2 172.31.1.1 [*] 214.085 ms 219.588 ms 235.012 ms
3 195.201.66.52 [AS24940] 223.928 ms 223.910 ms 234.972 ms
4 * * *
5 85.10.248.205 [AS24940] 235.876 ms 235.871 ms 85.10.250.253 [AS24940] 235.653 ms
6 213.239.208.221 [AS24940] 247.224 ms 85.10.250.209 [AS24940] 203.301 ms 213.239.208.221 [AS24940] 228.067 ms
7 213.239.252.21 [AS24940] 228.000 ms 213.239.245.250 [AS24940] 225.673 ms 240.931 ms
8 72.14.218.176 [AS15169] 239.249 ms 142.250.160.234 [AS15169] 307.365 ms 72.14.218.176 [AS15169] 240.167 ms
9 * * *
10 108.170.252.1 [AS15169] 315.941 ms 108.170.251.145 [AS15169] 252.236 ms 215.712 ms
11 108.170.251.145 [AS15169] 299.810 ms 299.787 ms 108.170.252.19 [AS15169] 290.106 ms
12 108.170.236.249 [AS15169] 246.007 ms * 108.170.236.120 [AS15169] 192.436 ms
13 209.85.142.167 [AS15169] 204.691 ms 209.85.245.231 [AS15169] 206.092 ms *
14 209.85.245.231 [AS15169] 259.016 ms * *
15 216.239.58.254 [AS15169] 300.078 ms * *
16 * 142.251.67.132 [AS15169] 334.793 ms 142.251.69.179 [AS15169] 386.770 ms
17 * 172.253.76.17 [AS15169] 349.484 ms *
18 216.239.56.228 [AS15169] 349.450 ms 74.125.252.49 [AS15169] 348.811 ms 72.14.239.197 [AS15169] 437.533 ms
19 74.125.252.47 [AS15169] 437.534 ms 216.239.56.228 [AS15169] 441.481 ms 74.125.252.49 [AS15169] 443.749 ms
20 * * *
21 * * *
22 * * *
23 * * *
24 * * *
25 * * *
26 * * *
27 * * *
28 * * *
29 * * *
30 * * *
31 * * *
32 * * *
33 * * *
34 * * *
35 * * *
36 * * *
37 * * *
38 * * *
39 * * *
40 * * *
41 * * *
42 * * *
43 * * *
44 * * *
45 * * *
46 * * *
47 * * *
48 * * *
49 * * *
50 * * *
# traceroute -n ooni.org --icmp -m50 -A
traceroute to ooni.org (104.198.14.52), 50 hops max, 60 byte packets
1 192.168.128.1 [*] 192.712 ms 202.952 ms 202.969 ms
2 172.31.1.1 [*] 215.994 ms 215.978 ms 215.988 ms
3 195.201.66.52 [AS24940] 215.990 ms 216.967 ms 225.389 ms
4 * * *
5 85.10.248.205 [AS24940] 234.141 ms 235.204 ms 235.846 ms
6 213.239.208.221 [AS24940] 235.206 ms 211.323 ms 210.436 ms
7 213.239.245.250 [AS24940] 209.800 ms 210.381 ms 209.806 ms
8 142.250.160.234 [AS15169] 296.548 ms 296.543 ms 296.527 ms
9 * * *
10 172.253.73.152 [AS15169] 299.174 ms 298.391 ms 290.207 ms
11 108.170.251.208 [AS15169] 290.171 ms 290.168 ms 291.686 ms
12 108.170.226.3 [AS15169] 282.384 ms 281.110 ms 280.447 ms
13 209.85.244.158 [AS15169] 293.000 ms 293.691 ms 293.679 ms
14 209.85.245.231 [AS15169] 303.117 ms 313.463 ms 314.110 ms
15 142.251.69.52 [AS15169] 375.580 ms 375.537 ms 375.580 ms
16 142.251.69.9 [AS15169] 394.030 ms 371.614 ms 377.574 ms
17 142.251.67.132 [AS15169] 391.349 ms 380.651 ms 386.538 ms
18 72.14.239.197 [AS15169] 419.132 ms 420.290 ms 420.783 ms
19 216.239.43.79 [AS15169] 420.196 ms 415.617 ms 418.509 ms
20 72.14.239.161 [AS15169] 428.967 ms 423.064 ms 407.262 ms
21 * * *
22 * * *
23 * * *
24 * * *
25 * * *
26 * * *
27 * * *
28 * * *
29 104.198.14.52 [AS396982/AS15169] 436.369 ms 450.152 ms 428.301 ms
# traceroute -n ooni.org --udp -m50 -O info --port=443 -A
traceroute to ooni.org (104.198.14.52), 50 hops max, 60 byte packets
1 192.168.128.1 [*] 196.894 ms 210.786 ms 210.780 ms
2 172.31.1.1 [*] 254.024 ms 255.827 ms 253.965 ms
3 195.201.66.52 [AS24940] 239.107 ms 239.076 ms 239.014 ms
4 * * *
5 85.10.248.205 [AS24940] 264.865 ms 85.10.250.253 [AS24940] 240.069 ms 254.244 ms
6 85.10.250.209 [AS24940] 254.224 ms 85.10.250.213 [AS24940] 212.183 ms 246.152 ms
7 213.239.252.21 [AS24940] 246.123 ms 213.239.245.254 [AS24940] 246.100 ms 213.239.252.21 [AS24940] 246.053 ms
8 72.14.218.176 [AS15169] 246.058 ms 248.892 ms 142.250.160.234 [AS15169] 316.783 ms
9 108.170.252.1 [AS15169] 248.839 ms 172.253.71.88 [AS15169] 249.109 ms 142.251.64.184 [AS15169] 248.730 ms
10 108.170.251.209 [AS15169] 260.839 ms 108.170.251.208 [AS15169] 280.100 ms 108.170.251.145 [AS15169] 211.933 ms
11 108.170.236.249 [AS15169] 212.686 ms 108.170.252.18 [AS15169] 290.697 ms 209.85.242.79 [AS15169] 211.847 ms
12 108.170.234.10 [AS15169] 208.306 ms * 209.85.240.113 [AS15169] 267.057 ms
13 209.85.245.231 [AS15169] 219.506 ms * 310.886 ms
14 209.85.142.167 [AS15169] 300.270 ms 142.251.69.52 [AS15169] 300.234 ms 301.500 ms
15 142.251.69.9 [AS15169] 310.781 ms 142.251.69.52 [AS15169] 368.404 ms 209.85.142.100 [AS15169] 382.030 ms
16 216.239.57.196 [AS15169] 371.146 ms * *
17 72.14.239.197 [AS15169] 359.696 ms 341.801 ms *
18 74.125.252.53 [AS15169] 353.315 ms 72.14.239.197 [AS15169] 432.218 ms 216.239.43.79 [AS15169] 351.941 ms
19 216.239.54.141 [AS15169] 351.295 ms 209.85.243.119 [AS15169] 361.653 ms 362.233 ms
20 * * *
21 * * *
22 * * *
23 * * *
24 * * *
25 * * *
26 * * *
27 * * *
28 * * *
29 104.198.14.52 [AS396982/AS15169] 342.698 ms 358.024 ms 358.215 ms
And this ban is bidirectional. This means that in some Google servers, you can not communicate with any Iranian IP. Like Google Cloud Shell:
$ traceroute --tcp --port=443 -O info -A -n iran.ir
traceroute to iran.ir (195.146.59.198), 30 hops max, 60 byte packets
1 172.17.0.1 [*] 0.059 ms 0.014 ms 0.012 ms
2 * * *
3 * * *
4 * * *
5 * * *
6 * * *
7 * * *
8 * * *
9 * * *
10 * * *
11 * * *
12 * * *
13 * * *
14 * * *
15 * * *
16 * * *
17 * * *
18 * * *
19 * * *
20 * * *
21 * * *
22 * * *
23 * * *
24 * * *
25 * * *
26 * * *
27 * * *
28 * * *
29 * * *
30 * * *
$ ping -c9 iran.ir
PING iran.ir (195.146.59.198) 56(84) bytes of data.
--- iran.ir ping statistics ---
9 packets transmitted, 0 received, 100% packet loss, time 232ms
In all of the above tests, censorship has not been imposed by the user government. However, in some cases, the user network may also block some of these addresses, which are blocked due to sanctions. The above tests are performed in a way that does not involve this censorship of the user government.
In such a situation, it is very difficult to distinguish between these two types of Internet censorship. As we at WikiCensorship strive to increase transparency, we will Investigate the various methods of censorship due to sanctions here, and if we have enough data, knowledge and techniques to distinguish them, we will publish it in a new post on Wikicensorship.