Harden-Runner provides network egress filtering and runtime security for GitHub-hosted and self-hosted runners.
Learn how Harden-Runner works through the video below, which shows how it detected a supply chain attack on a Google open-source project.
| CISA Explore |
Microsoft Explore |
Google Explore |
DataDog Explore |
Intel Explore |
Kubernetes Explore |
Node.js Explore |
AWS Explore |
There are two main threats from compromised workflows, dependencies, and build tools in a CI/CD environment:
- Exfiltration of CI/CD credentials and source code
- Tampering of source code, dependencies, or artifacts during the build to inject a backdoor
Harden-Runner monitors process, file, and network activity to:
| Countermeasure | Prevent Security Breach | |
|---|---|---|
| 1. | Monitor and block outbound network traffic at the DNS, HTTPS (Layer 7), and network layers (Layers 3 and 4) to prevent exfiltration of code and CI/CD credentials | To prevent the Codecov breach scenario |
| 2. | Detect if source code is being tampered during the build process to inject a backdoor | To detect the XZ Utils and SolarWinds incident scenario |
| 3. | Detect poisoned workflows and compromised dependencies | To detect Dependency confusion and Malicious dependencies |
-
Add the
step-security/harden-runnerGitHub Action to your GitHub Actions workflow file as the first step in each job.steps: - uses: step-security/harden-runner@63c24ba6bd7ba022e95695ff85de572c04a18142 # v2.7.0 with: egress-policy: audit
-
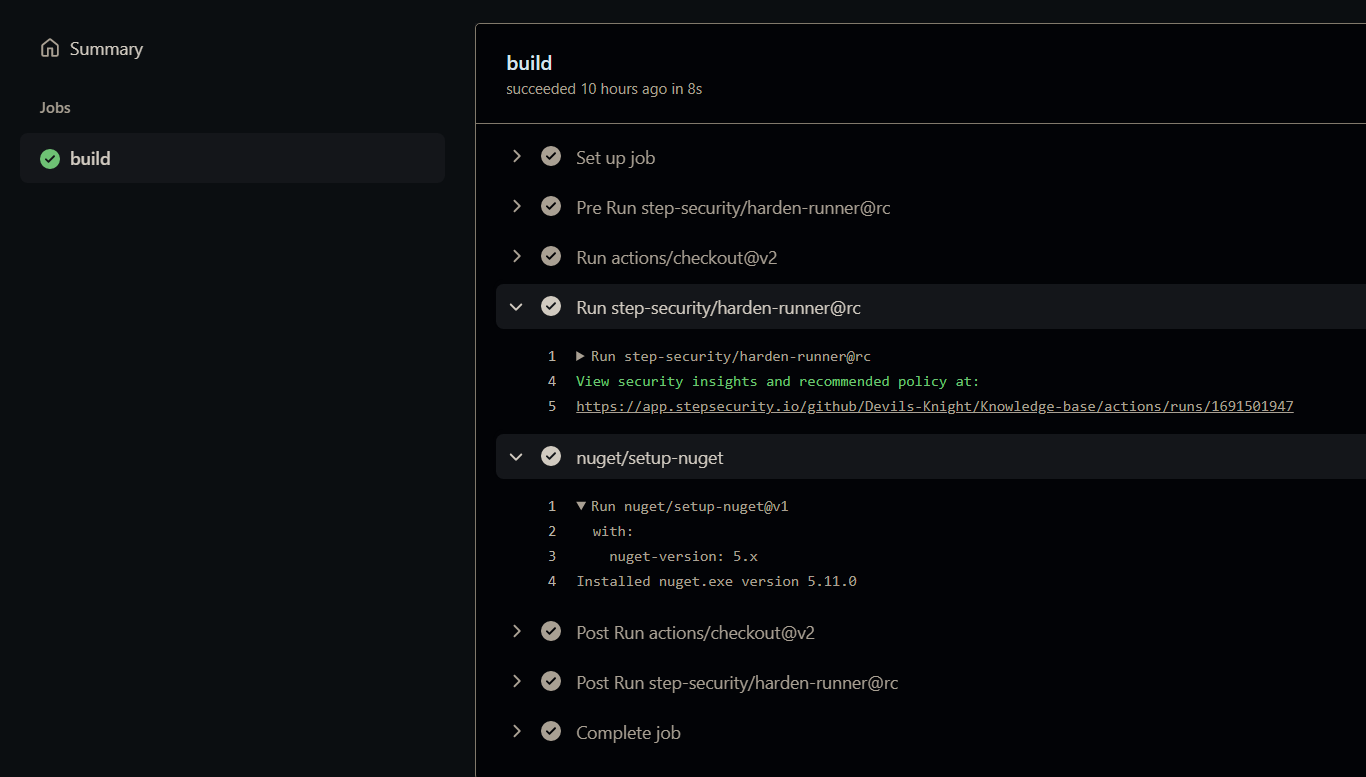
In the workflow logs and the job markdown summary, you will see a link to security insights and recommendations.
-
Click on the link (example link). You will see a process monitor view of network and file events correlated with each step of the job.
-
In the
Recommended Policytab, you'll find a recommended block policy based on outbound calls aggregated from the current and past runs of the job. You can update your workflow file with this policy, or alternatively, use the Policy Store to apply the policy without modifying the workflow file. From now on, any outbound calls not in the allowed list will be blocked.
You can use GitHub Actions Goat to try Harden-Runner. You only need a GitHub Account and a web browser.
Hands-on Tutorials for GitHub Actions Runtime Security:
Hardening for self-hosted runners and GitHub-hosted runners used in private repositories is supported with a commercial license. Check out the documentation for more details.
- To use Harden-Runner in a
Privaterepository, you must install the StepSecurity Actions Security GitHub App. - This is needed to access the GitHub Actions API and to authenticate users to access the insights URL for private repositories.
- If you use Harden-Runner GitHub Action in a private repository, the generated insights URL is NOT public. Only those who have access to the repository can view it.
Read this case study on how Kapiche uses Harden-Runner to improve software supply chain security in their private repositories.
Explore demo workflows using self-hosted ARC Runner and ARC Harden-Runner here.
Actions Runner Controller (ARC) is a Kubernetes operator that orchestrates self-hosted runners for GitHub Actions.
- Instead of adding the Harden-Runner GitHub Action in each job, you'll need to install the ARC Harden-Runner daemonset on your Kubernetes cluster.
- Upon installation, the ARC Harden-Runner daemonset monitors all jobs run on the cluster; you do NOT need to add the Harden-Runner GitHub Action to each job for
auditmode. You do need to add the Harden-Runner GitHub Action to jobs where you want to enableblockmode. - Please email [email protected] for instructions on how to install the ARC-Harden-Runner daemonset on your Kubernetes cluster.
Explore demo workflows using self-hosted VM Runners and Harden-Runner here.
- Instead of adding the Harden-Runner GitHub Action in each job, you'll need to install the Harden-Runner agent on your runner image (e.g. AMI). This is typically done using packer or as a post-install step when using the https://github.com/philips-labs/terraform-aws-github-runner project to setup runners.
- The Harden-Runner agent monitors all jobs run on the VM, both ephemeral and persistent runners are supported; you do NOT need to add the Harden-Runner GitHub Action to each job for
auditmode. You do need to add the Harden-Runner GitHub Action to jobs where you want to enableblockmode. - Please email [email protected] for instructions on how to install the Harden-Runner agent on your self-hosted VM runners. This agent is different than the one used for GitHub-hosted runners.
For details, check out the documentation at https://docs.stepsecurity.io
Applies to both GitHub-hosted and self-hosted runners
Harden-Runner monitors all outbound traffic from each job at the DNS and network layers
- After the workflow completes, each outbound call is correlated with each step of the job, and shown in the insights page
- For self-hosted runners, no changes are needed to workflow files to monitor egress traffic
- A filtering (block) egress policy is suggested in the insights page based on the current and past job runs
Applies to GitHub-hosted and self-hosted VM runners
Harden-Runner can monitor outbound HTTPS requests. This feature is supported with a commercial license.
- HTTPS events are monitored using eBPF (no MITM proxy is used)
- If a HTTP PUT/ POST/ PATCH call is made to
github.comorapi.github.comhosts to a HTTP Path with a different organization than where the workflow is running, the call is marked as anomalous - As of now, only HTTPS calls to
github.comandapi.github.comhosts are monitoried.
Applies to both GitHub-hosted and self-hosted runners
Harden-Runner creates a baseline of outbound traffic for each job during the first few runs that it monitors
- After the baseline is created, any new outbound destinations are marked as anomalous in the insights page
- You can view the list of all anomalous outbound network traffic in the
Runtime detectionspage on the dashboard
Applies to both GitHub-hosted and self-hosted runners
Once allowed endpoints are set in the policy in the workflow file, or in the Policy Store
- Harden-Runner blocks egress traffic at the DNS (Layer 7) and network layers (Layers 3 and 4)
- It blocks DNS exfiltration, where attacker tries to send data out using DNS resolution
- Wildcard domains are supported, e.g. you can add
*.data.mcr.microsoft.com:443to the allowed list, and egress traffic will be allowed toeastus.data.mcr.microsoft.com:443andwestus.data.mcr.microsoft.com:443
Applies to both GitHub-hosted and self-hosted runners
Harden-Runner monitors file writes and can detect if a file is overwritten.
- Source code overwrite is not expected in a release build
- All source code files are monitored, which means even changes to IaC files (Kubernetes manifest, Terraform) are detected
- You can enable notifications to get one-time alert when source code is overwritten
- For self-hosted runners, no changes are needed to workflow files for file monitoring
Applies to GitHub-hosted runners
GitHub-hosted runner uses passwordless sudo for running jobs.
- This means compromised build tools or dependencies can install attack tools
- If your job does not need sudo access, you see a policy recommendation to disable sudo in the insights page
- When you set
disable-sudototrue, the job steps run without sudo access to the GitHub-hosted Ubuntu VM
Applies to both GitHub-hosted and self-hosted runners
Install the StepSecurity Actions Security GitHub App to get security alerts.
- Email and Slack notifications are supported
- Notifications are sent when outbound traffic is blocked or source code is overwritten
- Notifications are not repeated for the same alert for a given workflow
- If you have questions or ideas, please use discussions.
- For support for self-hosted runners and private repositories, email [email protected].
- If you use a different CI/CD Provider (e.g. Jenkins, Gitlab CI, etc), and would like to use Harden Runner in your environment, please email [email protected]
For GitHub-hosted runners, Harden-Runner GitHub Action downloads and installs the StepSecurity Agent.
- The code to monitor file, process, and network activity is in the Agent.
- The agent is written in Go and is open source at https://github.com/step-security/agent
- The agent's build is reproducible. You can view the steps to reproduce the build here
- ARC Harden Runner daemonset uses eBPF
- You can find more details in this blog post: https://www.stepsecurity.io/blog/introducing-harden-runner-for-kubernetes-based-self-hosted-actions-runners
- ARC Harden Runner is NOT open source.
- For self-hosted VMs, you add the Harden-Runner agent into your runner image (e.g. AMI).
- Agent for self-hosted VMs is NOT open source.
- Only Ubuntu VM is supported. Windows and MacOS GitHub-hosted runners are not supported. There is a discussion about that here.
- Harden-Runner is not supported when job is run in a container as it needs sudo access on the Ubuntu VM to run. It can be used to monitor jobs that use containers to run steps. The limitation is if the entire job is run in a container. That is not common for GitHub Actions workflows, as most of them run directly on
ubuntu-latest. Note: This is not a limitation for Self-Hosted runners.
- Since ARC Harden Runner uses eBPF, only Linux jobs are supported. Windows and MacOS jobs are not supported.
- Only Ubuntu VM is supported. Windows and MacOS jobs are not supported.