This project demonstrates the deployment of a three-tier web application on AWS, including setting up networking, application components, load balancing, and database configuration.
This project involves:
- 🏗️ Creating a Virtual Private Cloud (VPC) and subnets.
- 🌐 Configuring Internet and NAT gateways.
- 🚀 Deploying EC2 instances for web and application servers.
- ⚖️ Setting up an Application Load Balancer (ALB).
- 🗄️ Configuring an RDS MySQL database.
- 🛠️ Installing and configuring Apache, PHP, and phpMyAdmin.
here's a flowchart outlining the main steps involved in deploying the AWS 3-Tier Web Application:
graph TD;
A[Start] --> B{Networking Setup}
B --> C[Create VPC]
B --> D[Create Subnets]
B --> E[Create Internet Gateway]
B --> F[Create NAT Gateway]
B --> G[Create Route Tables]
B --> H[Create Security Groups]
B --> I[Configure Network ACLs]
B --> J{Application Components Deployment}
J --> K[Launch EC2 Instances]
J --> L[Install Software]
J --> M[Configure Services]
J --> N[Deploy Application Code]
J --> O{Load Balancer Configuration}
O --> P[Create ALB]
O --> Q[Create Target Groups]
O --> R[Register Targets]
O --> S[Create Listener]
O --> T[Configure Health Checks]
J --> U{Database Setup}
U --> V[Create RDS Instance]
U --> W[Configure Security Groups]
U --> X[Configure Parameter Groups]
U --> Y[Connect Application to Database]
J --> Z{Testing and Validation}
Z --> AA[Test Application Accessibility]
Z --> AB[Test Database Connectivity]
Z --> AC[Perform Load Testing]
Z --> AD[Monitor Performance]
Z --> AE[Verify High Availability]
A --> AF[Cleanup]
AF --> AG[Delete Resources]
AG --> AH[Terminate Instances]
AG --> AI[Delete Subnets]
AG --> AJ[Delete VPC]
AG --> AK[Delete Load Balancer]
AG --> AL[Delete RDS Instance]
AG --> AM[Delete Other Resources]
AF --> AN[End]
This flowchart provides an overview of the steps involved in setting up the network, deploying application components, configuring the load balancer, setting up the database, testing and validating the deployment, and finally cleaning up the resources.
- 🧑💻 AWS account
- 📚 Basic knowledge of AWS services
- 💻 SSH client for connecting to EC2 instances
-
Create a VPC
-
Create Subnets
- Three public subnets (one in each availability zone):
172.20.1.0/24172.20.2.0/24172.20.3.0/24
- Three private application subnets (one in each availability zone):
172.20.4.0/24172.20.5.0/24172.20.6.0/24
- Three private database subnets (one in each availability zone):
- Three public subnets (one in each availability zone):
-
Configure Gateways
- Create and attach an Internet Gateway to the VPC.
- Create a NAT Gateway in one of the public subnets with an Elastic IP.
-
Create Route Tables
- Create and associate route tables for public, application, and database subnets.
- Configure routes for the Internet Gateway and NAT Gateway.
-
Deploy EC2 Instances
-
Install Software
- SSH into the Jump Server, then connect to the PHP App Servers.
- Install PHP and Apache on the PHP App Servers.
- Configure Apache and install phpMyAdmin for database management.
- Create Application Load Balancer (ALB)
-
Create RDS Instance
-
Configure phpMyAdmin
- Modify the phpMyAdmin configuration to connect to the RDS instance.
- Enable session stickiness on the target group to handle stateful sessions.
- Verify the proper functioning of the Apache server and load balancing.
- Test phpMyAdmin access and database connection.
- 🏗️ VPC
- 📂 Subnets (Public, Application, Database)
- 🌐 Internet Gateway
- 🌍 NAT Gateway
- 🛤️ Route Tables
- 🖥️ EC2 Instances (Jump Server, PHP App Servers)
- ⚖️ Application Load Balancer
- 🗄️ RDS MySQL Database
This project demonstrates a comprehensive setup of a 3-tier web application on AWS, providing a scalable and resilient architecture suitable for various web applications.
Step by Step guid
# AWS 3-Tier Web Application Deployment
This project demonstrates the deployment of a highly available and scalable three-tier web application architecture on AWS, consisting of a web tier, application tier, and database tier.
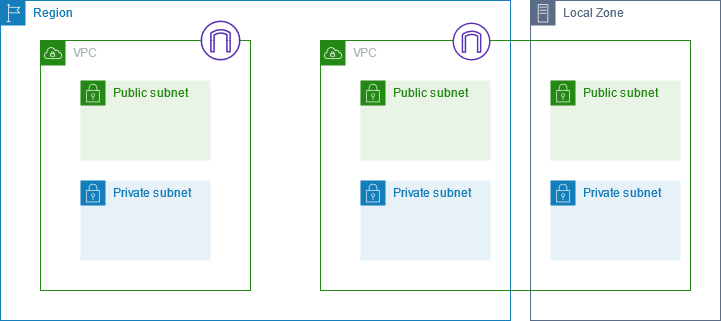
## Architecture Overview

The architecture includes the following components:
1. Virtual Private Cloud (VPC): Isolated virtual network for the application.
2. Subnets: Public, private application, and private database subnets across multiple Availability Zones (AZs) for high availability.
3. Internet Gateway: Provides internet access to resources in the public subnets.
4. NAT Gateway: Allows resources in private subnets to access the internet.
5. Web Servers: Two EC2 instances running Apache and PHP in the private application subnets.
6. Application Load Balancer (ALB): Distributes traffic across the web servers in the public subnets.
7. RDS MySQL Database: A Multi-AZ RDS MySQL database instance in the private database subnets for high availability.
## Prerequisites
- AWS account
- AWS CLI installed and configured
- SSH client (e.g., PuTTY for Windows, Terminal for macOS/Linux)
## Step-by-Step Deployment
### 1. Networking Setup
1. Create a VPC:
```bash
aws ec2 create-vpc --cidr-block 172.20.0.0/16-
Create public subnets:
aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.1.0/24 --availability-zone <region-az1> aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.2.0/24 --availability-zone <region-az2> aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.3.0/24 --availability-zone <region-az3>
-
Create private application subnets:
aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.4.0/24 --availability-zone <region-az1> aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.5.0/24 --availability-zone <region-az2> aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.6.0/24 --availability-zone <region-az3>
-
Create private database subnets:
aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.7.0/24 --availability-zone <region-az1> aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.8.0/24 --availability-zone <region-az2> aws ec2 create-subnet --vpc-id <vpc-id> --cidr-block 172.20.9.0/24 --availability-zone <region-az3>
-
Create an Internet Gateway and attach it to the VPC:
aws ec2 create-internet-gateway aws ec2 attach-internet-gateway --vpc-id <vpc-id> --internet-gateway-id <igw-id>
-
Create a NAT Gateway in one of the public subnets with an Elastic IP:
aws ec2 allocate-address --domain vpc aws ec2 create-nat-gateway --subnet-id <public-subnet-id> --allocation-id <eip-allocation-id>
-
Create and associate Route Tables:
-
Public Route Table:
aws ec2 create-route-table --vpc-id <vpc-id> aws ec2 associate-route-table --subnet-id <public-subnet-id> --route-table-id <rtb-id> aws ec2 create-route --route-table-id <rtb-id> --destination-cidr-block 0.0.0.0/0 --gateway-id <igw-id>
-
Private Application Route Table:
aws ec2 create-route-table --vpc-id <vpc-id> aws ec2 associate-route-table --subnet-id <private-app-subnet-id> --route-table-id <rtb-id> aws ec2 create-route --route-table-id <rtb-id> --destination-cidr-block 0.0.0.0/0 --nat-gateway-id <nat-gw-id>
-
Private Database Route Table:
aws ec2 create-route-table --vpc-id <vpc-id> aws ec2 associate-route-table --subnet-id <private-db-subnet-id> --route-table-id <rtb-id> aws ec2 create-route --route-table-id <rtb-id> --destination-cidr-block 0.0.0.0/0 --nat-gateway-id <nat-gw-id>
-
-
Launch an EC2 instance (Jump Server) in the public subnet:
aws ec2 run-instances --image-id <amazon-linux-ami-id> --instance-type t2.micro --key-name <your-key-pair> --security-group-ids <jump-server-sg-id> --subnet-id <public-subnet-id>
-
Launch two EC2 instances (PHP App Servers) in the private application subnets:
aws ec2 run-instances --image-id <amazon-linux-ami-id> --instance-type t2.micro --key-name <your-key-pair> --security-group-ids <web-server-sg-id> --subnet-id <private-app-subnet-id-1> aws ec2 run-instances --image-id <amazon-linux-ami-id> --instance-type t2.micro --key-name <your-key-pair> --security-group-ids <web-server-sg-id> --subnet-id <private-app-subnet-id-2>
-
SSH into the Jump Server and then connect to the PHP App Servers.
-
Install Apache, PHP, and phpMyAdmin on the PHP App Servers:
sudo yum update -y sudo amazon-linux-extras install -y lamp-mariadb10.2-php7.2 php7.2 sudo yum install -y phpmyadmin
-
Configure Apache and phpMyAdmin:
-
Edit the Apache configuration file
/etc/httpd/conf/httpd.confand add the following line at the end of the<IfModule dir_module>section:DirectoryIndex index.php index.html -
Edit the phpMyAdmin configuration file
/etc/httpd/conf.d/phpMyAdmin.confand update theRequireline to allow access from the ALB's security group:Require ip <alb-security-group-cidr> -
Restart Apache:
sudo systemctl restart httpd
-
-
Create an Application Load Balancer (ALB) in the public subnets:
aws elbv2 create-load-balancer --name <load-balancer-name> --subnets <public-subnet-id-1> <public-subnet-id-2> <public-subnet-id-3> --security-groups <alb-security-group-id>
-
Create a Target Group for the PHP App Servers:
aws elbv2 create-target-group --name <target-group-name> --protocol HTTP --port 80 --vpc-id <vpc-id>
-
Register the PHP App Servers as targets:
aws elbv2 register-targets --target-group-arn <target-group-arn> --targets Id=<php-app-server-id-1> Id=<php-app-server-id-2>
-
Create a Listener for the ALB:
aws elbv2 create-listener --load-balancer-arn <load-balancer-arn> --protocol HTTP --port 80 --default-actions Type=forward,TargetGroupArn=<target-group-arn>
-
Create an RDS MySQL instance in the private database subnets:
aws rds create-db-instance --db-instance-identifier <db-instance-identifier> --db-instance-class db.t2.micro --engine mysql --allocated-storage 20 --master-username <master-username> --master-user-password <master-password> --vpc-security-group-ids <rds-sg-id> --db-subnet-group-name <db-subnet-group-name> --multi-az
-
Configure security groups and parameter groups as necessary.
-
Configure the PHP application to connect to the RDS MySQL database:
- Update the database configuration file of your PHP application with the RDS endpoint, username, and password.
-
Deploy the PHP application code to the PHP App Servers.
-
Access the application via the ALB's DNS name:
- Obtain the ALB DNS name from the AWS Management Console or via CLI.
aws el