In this repository, we host Difuzer, a static logic bomb detector. Difuzer relies on static inter-procedural taint analysis to find sensitive trigger entry-points in Android apps. It is able to filter abnormal triggers known as Hidden Sensitive Operations from trigger-specific features.
git clone https://github.com/JordanSamhi/Difuzer.git
cd Difuzer mvn clean install:install-file -Dfile=libs/soot-infoflow-android-classes.jar -DgroupId=de.tud.sse -DartifactId=soot-infoflow-android -Dversion=2.7.1 -Dpackaging=jar mvn clean install:install-file -Dfile=libs/soot-infoflow-classes.jar -DgroupId=de.tud.sse -DartifactId=soot-infoflow -Dversion=2.7.1 -Dpackaging=jar mvn clean install
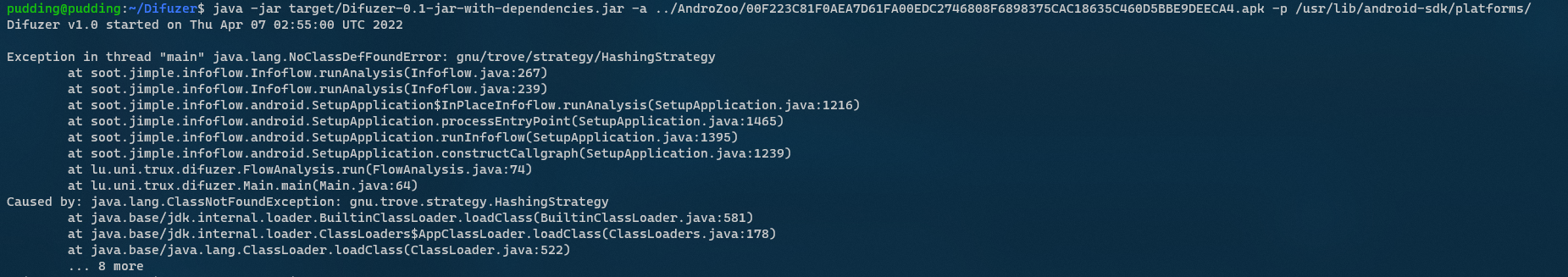
java -jar Difuzer/target/Difuzer-0.1-jar-with-dependencies.jar options
Options:
-a: The path to the APK to process.-p: The path to Android platofrms folder.-r: Displays raw results.-t: Set the timeout of the analysis.-e: Set an EasyTaintWrapper file.
- Maven - Dependency Management
This project is licensed under the Apache License 2.0 - see the LICENSE file for details
For any question regarding this study, please contact us at: Jordan Samhi