Vouch Zero Password is a blockchain-based identity solution that completely eliminates passwords.
Vouch Zero Password utilizes a user’s smart device and biometrics to securely conduct Identity Creation, Verification, Authentication and Authorization.
Login is as simple as picking up your smart device.
There are no passwords to remember and no hardware keys required.
Vouch distributed, blockchain-based security model completely eliminates digital identity theft and reduces system vulnerabilities.
In order to complete this evaluation, you will first need to contact Vouch to provision the Remote IdP side of the Federation and then simply download the Vouch Zero Password mobile app for the biometric enrollment and authentication.
Please contact us at [email protected] to get started or for more information.
- You are familiar with ForgeRock Federation concepts and have access to the AM SAML v2.0 Guide.
- You have engaged with Vouch, and received an email with a file named
vouch-idp-metadata.xmlas attachment
This section will guide you through the steps required for configuring AM with Vouch Zero Password (VZP) and trying it out for the first time.
The following procedure provides steps for creating a hosted service provider by using the Create Hosted Service Provider wizard. Afterwards, you will update the Service Provider configuration with VZP settings.
- Under
Realms > Realm Name > Dashboard > Configure SAMLv2 Provider, clickCreate Hosted Service Provider. Name: Provide your own unique identifier or leave the default suggested name (for exampleVZP-CoT)- Circle of Trust: Select
Add to newoption and provide a unique name to create a new Circle of Trust. - Attribute Mapping : leave
use default attribute mapping from Identity providerchecked for now - Click the
Configurebutton - In the follow up dialog asking to create the remote identity provider, select
No.
- Navigate to
Applications -> Federation -> Entity Providers - Select the newly created hosted SP entry
- in the
NameID Formatsection, leave the defaulturn:oasis:names:tc:SAML:1.1:nameid-format:unspecified - in the
Authentication Contextsection, setSoftwarePKIas theDefault Authentication Context - Navigate to the
Assertion Processingtab- in the
Attribute Mappersection, add an entry to Current Values to map the incomingVouchIdentifierassertion to a stable identifier in the AM user data store. (egVouchIdentitifer=uid) - in the
Auto Federationsection, checkEnabledand set theAttributetoVouchIdentifier
- in the
- Navigate to the
Servicestab- in the
Assertion Consumer Servicesection, checkHTTP-POSTand replace the the/Consumer/string part to/AuthConsumer. ( seeTo Implement SAML v2.0 SSO in Integrated Modein the AMSAML v2.0 Guidefor more info )
- in the
In this section you will add VZP as a Remote Identity Provider and add it to newly created CoT.
You will need the vouch-idp-metadata.xml file from the VZP server ( see Prerequisites )
- Under
Realms > Realm Name > Dashboard > Configure SAMLv2 Provider, clickConfigure Remote Identity Provider. - upload the
vouch-idp-metadata.xmlfile - in the
Circle of Trustsection, selectExisting Circle of Trust: Select the CoT you have created as instructed in the Create a Hosted SP section. - Click
Configure
In this section you will create a new SAML2 authentication module and an authentication chain to redirect authentication to VZP.
- In the realm starting page of the AM admin console, navigate through
Authentication-ModulesandAdd a Module - Specify a
Name(exampleVZP), selectSAML2asTypeand clickCreate - Configure the SAML2 authentication module options:
- Set
IdP Entity IDto the value defined by theentityIDattribute in thevouch-idp-metadata.xmlfile. - Set
SP MetaAliasto the MetaAlias of your previously created hosted SP (eg/sp) - Set
Request BindingtoHTTP-Redirect. - Set
Response BindingtoHTTP-POST - Set
NameID Formattourn:oasis:names:tc:SAML:1.1:nameid-format:unspecified
- Set
- Navigate to
Realms > Realm Name > Authentication > Chains, clickAdd Chain - Specify a
Name(exampleVZPChain) and clickCreate - Click
Add Module - In the New Module dialog:
- Under
Select Module, select the module created above (egVZP) - Under
Select Criteria, selectRequired
- Under
- Click
OKand thenSave Changes
In this section you will test your configuration by logging in to the AM console as a user to view that user’s profile. You will be redirected to the VZP IdP for a passwordless authentication using your mobile device and your biometrics.
- Download the VZP mobile app from the Apple or Google Play App Store
- Open the invitation sms sent by your Vouch contact, and click the link
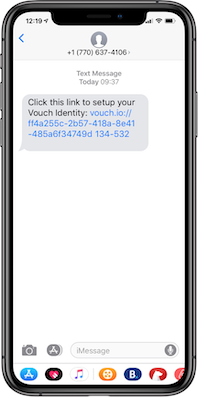
- This opens the app, the user will then allow any requested permissions



Note: The flow above demonstrates a default onboarding process of the first user via an sms invitation. Many other mechanisms including email and in-person endorsements are supported as well, please contact Vouch for more info.
- Clear your browser's cache and cookies.
- Login into the user’s profile using a URL that references the authentication chain with SAML2 module that you created above. For example, http://openam.partner.com:8080/openam/XUI/#login/&service=VZPChain
- If configured correctly, AM will redirect you to the VZP identity provider for authentication. You will be presented with a page similar to the one below:

- In the VZP app tap
SCAN QR

- Scan the QR code and then present your biometrics
- AM should now give you access to the user’s profile page.
Note: The QR code is only used initially to bind the browser to the mobile device, subsequent logins will send out a push notification, reducing user friction while preserving strong security.
For assistance or more information, please contact us at [email protected]


