bitbar / test-samples Goto Github PK
View Code? Open in Web Editor NEWSample test scripts and applications for Bitbar Cloud
Home Page: https://docs.bitbar.com/testing/index.html
License: Apache License 2.0
Sample test scripts and applications for Bitbar Cloud
Home Page: https://docs.bitbar.com/testing/index.html
License: Apache License 2.0
Xerces2 is the next generation of high performance, fully compliant XML parsers in the Apache Xerces family. This new version of Xerces introduces the Xerces Native Interface (XNI), a complete framework for building parser components and configurations that is extremely modular and easy to program.
The Apache Xerces2 parser is the reference implementation of XNI but other parser components, configurations, and parsers can be written using the Xerces Native Interface. For complete design and implementation documents, refer to the XNI Manual.
Xerces2 is a fully conforming XML Schema 1.0 processor. A partial experimental implementation of the XML Schema 1.1 Structures and Datatypes Working Drafts (December 2009) and an experimental implementation of the XML Schema Definition Language (XSD): Component Designators (SCD) Candidate Recommendation (January 2010) are provided for evaluation. For more information, refer to the XML Schema page.
Xerces2 also provides a complete implementation of the Document Object Model Level 3 Core and Load/Save W3C Recommendations and provides a complete implementation of the XML Inclusions (XInclude) W3C Recommendation. It also provides support for OASIS XML Catalogs v1.1.
Xerces2 is able to parse documents written according to the XML 1.1 Recommendation, except that it does not yet provide an option to enable normalization checking as described in section 2.13 of this specification. It also handles namespaces according to the XML Namespaces 1.1 Recommendation, and will correctly serialize XML 1.1 documents if the DOM level 3 load/save APIs are in use.</p>
Library home page: https://xerces.apache.org/xerces2-j/
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/xerces/xercesImpl/2.11.0/xercesImpl-2.11.0.jar,/home/wss-scanner/.m2/repository/xerces/xercesImpl/2.11.0/xercesImpl-2.11.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A flaw was found in Wildfly's implementation of Xerces, specifically in the way the XMLSchemaValidator class in the JAXP component of Wildfly enforced the "use-grammar-pool-only" feature. This flaw allows a specially-crafted XML file to manipulate the validation process in certain cases. This issue is the same flaw as CVE-2020-14621, which affected OpenJDK, and uses a similar code. This flaw affects all Xerces JBoss versions before 2.12.0.SP3.
Publish Date: 2020-09-17
URL: CVE-2020-14338
Base Score Metrics:
Type: Upgrade version
Origin: https://bugzilla.redhat.com/show_bug.cgi?id=1860054
Release Date: 2020-07-21
Fix Resolution: xerces:xercesImpl:2.12.0.SP3
JUnit is a unit testing framework for Java, created by Erich Gamma and Kent Beck.
Library home page: http://junit.org
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: canner/.m2/repository/junit/junit/4.12/junit-4.12.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
In JUnit4 from version 4.7 and before 4.13.1, the test rule TemporaryFolder contains a local information disclosure vulnerability. On Unix like systems, the system's temporary directory is shared between all users on that system. Because of this, when files and directories are written into this directory they are, by default, readable by other users on that same system. This vulnerability does not allow other users to overwrite the contents of these directories or files. This is purely an information disclosure vulnerability. This vulnerability impacts you if the JUnit tests write sensitive information, like API keys or passwords, into the temporary folder, and the JUnit tests execute in an environment where the OS has other untrusted users. Because certain JDK file system APIs were only added in JDK 1.7, this this fix is dependent upon the version of the JDK you are using. For Java 1.7 and higher users: this vulnerability is fixed in 4.13.1. For Java 1.6 and lower users: no patch is available, you must use the workaround below. If you are unable to patch, or are stuck running on Java 1.6, specifying the java.io.tmpdir system environment variable to a directory that is exclusively owned by the executing user will fix this vulnerability. For more information, including an example of vulnerable code, see the referenced GitHub Security Advisory.
Publish Date: 2020-10-12
URL: CVE-2020-15250
Base Score Metrics:
Type: Upgrade version
Origin: GHSA-269g-pwp5-87pp
Release Date: 2020-07-21
Fix Resolution: junit:junit:4.13.1
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the commons-dbcp (1.4) jar in the classpath, and an attacker can find an RMI service endpoint to access, it is possible to make the service execute a malicious payload. This issue exists because of org.apache.commons.dbcp.datasources.SharedPoolDataSource and org.apache.commons.dbcp.datasources.PerUserPoolDataSource mishandling.
Publish Date: 2019-10-01
URL: CVE-2019-16942
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-16942
Release Date: 2019-10-01
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.6.7.3,2.7.9.7,2.8.11.5,2.9.10.1
A collection of various utility classes to ease working with strings, files, command lines, XML and more.
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/org/codehaus/plexus/plexus-utils/2.0.6/plexus-utils-2.0.6.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
Plexus-utils before 3.0.16 is vulnerable to command injection because it does not correctly process the contents of double quoted strings.
Publish Date: 2018-01-03
URL: CVE-2017-1000487
Base Score Metrics:
Type: Upgrade version
Origin: https://nvd.nist.gov/vuln/detail/CVE-2017-1000487
Release Date: 2018-01-03
Fix Resolution: 3.0.16
Command line parsing
Library home page: http://jcommander.org
Path to dependency file: test-samples/samples/testng-parallel-mobile-tests/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/beust/jcommander/1.72/jcommander-1.72.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
Inclusion of Functionality from Untrusted Control Sphere vulnerability found in jcommander before 1.75. jcommander resolving dependencies over HTTP instead of HTTPS.
Publish Date: 2019-02-19
URL: WS-2019-0490
Base Score Metrics:
Type: Upgrade version
Origin: cbeust/jcommander#465
Release Date: 2019-02-19
Fix Resolution: com.beust:jcommander:1.75
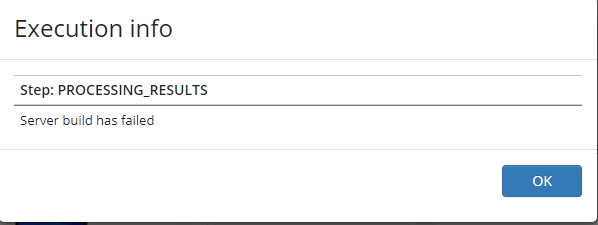
When trying to execute test on device on which the user doe's not have a subscription for, the test fails due to null pointer exception.
The user needs to debug the code in order to understand that the failure reason is "Resource is in invalid state: Failed to submit test run! No active subscription plan to run tests on selected devices."
I run Image Recognition Sample in Linux, has an error:"libopencv_java2413.so: libavcodec.so.53: cannot open shared object file: No such file or directory. "
When I call takeScreenshot() method ., it's working fine, and able to receive the screenshot in the desired path ., But when I call the method like findImageOnScreen() or tapImageOnScreen() which recalls takeScreenshot() method is getting an issue at screenshot2 with javaIOexeception which it works earlier.
Project Link:- https://github.com/bitbar/test-samples/tree/master/samples/testing-frameworks/appium/server-side/image-recognition
Device :- Google Pixel
Kindly refer to the error log below
error logs
java.io.IOException: Cannot run program "screenshot2": error=20, Not a directory
at java.lang.ProcessBuilder.start(ProcessBuilder.java:1048)
at java.lang.Runtime.exec(Runtime.java:620)
at java.lang.Runtime.exec(Runtime.java:485)
at imagerecognition.ImageRecognition.takeAndroidScreenshot(ImageRecognition.java:250)
at imagerecognition.ImageRecognition.takeScreenshot(ImageRecognition.java:235)
at imagerecognition.ImageRecognition.findImageLoop(ImageRecognition.java:199)
at imagerecognition.ImageRecognition.findImageOnScreen(ImageRecognition.java:184)
at TestdroidImageRecognition.findImageOnScreen(TestdroidImageRecognition.java:140)
at TestdroidImageRecognition.tapImageOnScreen(TestdroidImageRecognition.java:162)
at TestdroidImageRecognition.tapImageOnScreen(TestdroidImageRecognition.java:185)
at AppiumExxec.mainPageTest(AppiumExxec.java:61)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:62)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:498)
at org.junit.runners.model.FrameworkMethod$1.runReflectiveCall(FrameworkMethod.java:50)
at org.junit.internal.runners.model.ReflectiveCallable.run(ReflectiveCallable.java:12)
at org.junit.runners.model.FrameworkMethod.invokeExplosively(FrameworkMethod.java:47)
at org.junit.internal.runners.statements.InvokeMethod.evaluate(InvokeMethod.java:17)
at org.junit.rules.TestWatcher$1.evaluate(TestWatcher.java:55)
at org.junit.rules.RunRules.evaluate(RunRules.java:20)
at org.junit.runners.ParentRunner.runLeaf(ParentRunner.java:325)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:78)
at org.junit.runners.BlockJUnit4ClassRunner.runChild(BlockJUnit4ClassRunner.java:57)
at org.junit.runners.ParentRunner$3.run(ParentRunner.java:290)
at org.junit.runners.ParentRunner$1.schedule(ParentRunner.java:71)
at org.junit.runners.ParentRunner.runChildren(ParentRunner.java:288)
at org.junit.runners.ParentRunner.access$000(ParentRunner.java:58)
at org.junit.runners.ParentRunner$2.evaluate(ParentRunner.java:268)
at org.junit.internal.runners.statements.RunBefores.evaluate(RunBefores.java:26)
at org.junit.internal.runners.statements.RunAfters.evaluate(RunAfters.java:27)
at org.junit.runners.ParentRunner.run(ParentRunner.java:363)
at org.junit.runner.JUnitCore.run(JUnitCore.java:137)
at com.intellij.junit4.JUnit4IdeaTestRunner.startRunnerWithArgs(JUnit4IdeaTestRunner.java:68)
at com.intellij.rt.execution.junit.IdeaTestRunner$Repeater.startRunnerWithArgs(IdeaTestRunner.java:47)
at com.intellij.rt.execution.junit.JUnitStarter.prepareStreamsAndStart(JUnitStarter.java:242)
at com.intellij.rt.execution.junit.JUnitStarter.main(JUnitStarter.java:70)
Caused by: java.io.IOException: error=20, Not a directory
at java.lang.UNIXProcess.forkAndExec(Native Method)
at java.lang.UNIXProcess.<init>(UNIXProcess.java:247)
at java.lang.ProcessImpl.start(ProcessImpl.java:134)
at java.lang.ProcessBuilder.start(ProcessBuilder.java:1029)
master POM
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/org/apache/ant/ant/1.9.6/ant-1.9.6.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
As mitigation for CVE-2020-1945 Apache Ant 1.10.8 changed the permissions of temporary files it created so that only the current user was allowed to access them. Unfortunately the fixcrlf task deleted the temporary file and created a new one without said protection, effectively nullifying the effort. This would still allow an attacker to inject modified source files into the build process.
Publish Date: 2020-10-01
URL: CVE-2020-11979
Base Score Metrics:
Type: Upgrade version
Origin: https://ant.apache.org/security.html
Release Date: 2020-07-21
Fix Resolution: org.apache.ant:ant:1.10.9
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
FasterXML jackson-databind 2.x before 2.9.7 might allow remote attackers to conduct server-side request forgery (SSRF) attacks by leveraging failure to block the axis2-jaxws class from polymorphic deserialization.
Publish Date: 2019-01-02
URL: CVE-2018-14721
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-14721
Release Date: 2019-01-02
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.7,2.8.11.3,2.7.9.5,2.6.7.3
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariDataSource. This is a different vulnerability than CVE-2019-14540.
Publish Date: 2019-09-15
URL: CVE-2019-16335
Base Score Metrics:
Type: Upgrade version
Origin: https://github.com/FasterXML/jackson-databind/blob/master/release-notes/VERSION-2.x
Release Date: 2019-09-15
Fix Resolution: 2.9.10
Google OAuth Client Library for Java. Functionality that works on all supported Java platforms, including Java 5 (or higher) desktop (SE) and web (EE), Android, and Google App Engine.
Library home page: http://code.google.com/p/google-oauth-java-client/
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/google/oauth-client/google-oauth-client/1.15.0-rc/google-oauth-client-1.15.0-rc.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
PKCE support is not implemented in accordance with the RFC for OAuth 2.0 for Native Apps. Without the use of PKCE, the authorization code returned by an authorization server is not enough to guarantee that the client that issued the initial authorization request is the one that will be authorized. An attacker is able to obtain the authorization code using a malicious app on the client-side and use it to gain authorization to the protected resource. This affects the package com.google.oauth-client:google-oauth-client before 1.31.0.
Publish Date: 2020-07-09
URL: CVE-2020-7692
Base Score Metrics:
Type: Upgrade version
Origin: googleapis/google-oauth-java-client#470
Release Date: 2020-07-09
Fix Resolution: com.google.oauth-client:google-oauth-client:1.31.0
Core Jackson abstractions, basic JSON streaming API implementation
Library home page: https://github.com/FasterXML/jackson-core
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-core/2.6.0/jackson-core-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
OutOfMemoryError when writing BigDecimal In Jackson Core before version 2.7.7.
When enabled the WRITE_BIGDECIMAL_AS_PLAIN setting, Jackson will attempt to write out the whole number, no matter how large the exponent.
Publish Date: 2016-08-25
URL: WS-2018-0125
Type: Upgrade version
Origin: https://github.com/FasterXML/jackson-core/releases/tag/jackson-core-2.7.7
Release Date: 2016-08-25
Fix Resolution: com.fasterxml.jackson.core:jackson-core:2.7.7
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
FasterXML jackson-databind 2.x before 2.9.7 might allow attackers to conduct external XML entity (XXE) attacks by leveraging failure to block unspecified JDK classes from polymorphic deserialization.
Publish Date: 2019-01-02
URL: CVE-2018-14720
Base Score Metrics:
Type: Upgrade version
Origin: https://nvd.nist.gov/vuln/detail/CVE-2018-14720
Release Date: 2019-01-02
Fix Resolution: 2.9.7
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
FasterXML jackson-databind 2.0.0 through 2.9.10.2 lacks certain xbean-reflect/JNDI blocking, as demonstrated by org.apache.xbean.propertyeditor.JndiConverter.
Publish Date: 2020-02-10
URL: CVE-2020-8840
Base Score Metrics:
Type: Upgrade version
Origin: FasterXML/jackson-databind#2620
Release Date: 2020-02-10
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.3
Dear Sir,
I clone the sample project and run Java iOS test sample in command line, and maven console came that ERROR, but TestDriod sent out a email that the test finished.
Could you provide the what is problem in error?
command run:
mvn clean test -Dtest=com.testdroid.appium.ios.sample.SampleAppiumiOSTest
and got the error message:
Running com.testdroid.appium.ios.sample.SampleAppiumiOSTest
response:{"status":0,"sessionId":"9b3c88ec-0c1a-436e-8c8a-45742cf57065","value":{"message":"uploads successful","uploadCount":1,"rejectCount":0,"expiresIn":1800,"uploads":{"file":"9b3c88ec-0c1a-436e-8c8a-45742cf57065/BitbarIOSSample.ipa"},"rejects":{}}}
File id:4d6bb297-00ac-4fba-9a4c-bb9afa6fc920/BitbarIOSSample.ipa
Capabilities:Capabilities [{testdroid_password=xxxx, testdroid_description=Appium project description, app=com.bitbar.testdroid.BitbarIOSSample, testdroid_app=4d6bb297-00ac-4fba-9a4c-bb9afa6fc920/BitbarIOSSample.ipa, testdroid_target=iOS, testdroid_project=SHOPPO iOS, [email protected], testdroid_device=iPad 3 A1416 8.2, platformName=iOS, device=iphone, deviceName=iOS Phone, testdroid_testrun=iOS Run}]
Tests run: 1, Failures: 0, Errors: 1, Skipped: 0, Time elapsed: 11.97 sec <<< FAILURE!
Results :
Tests in error:
com.testdroid.appium.ios.sample.SampleAppiumiOSTest: com.testdroid.api.APIException: 400 Bad Request
Tests run: 1, Failures: 0, Errors: 1, Skipped: 0
The Apache Commons Codec package contains simple encoder and decoders for various formats such as Base64 and Hexadecimal. In addition to these widely used encoders and decoders, the codec package also maintains a collection of phonetic encoding utilities.
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-codec/commons-codec/1.10/commons-codec-1.10.jar
Dependency Hierarchy:
The Apache Commons Codec package contains simple encoder and decoders for various formats such as Base64 and Hexadecimal. In addition to these widely used encoders and decoders, the codec package also maintains a collection of phonetic encoding utilities.
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/java/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-codec/commons-codec/1.9/commons-codec-1.9.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
Apache commons-codec before version “commons-codec-1.13-RC1” is vulnerable to information disclosure due to Improper Input validation.
Publish Date: 2019-05-20
URL: WS-2019-0379
Base Score Metrics:
Type: Upgrade version
Origin: apache/commons-codec@48b6157
Release Date: 2019-05-12
Fix Resolution: 1.13-RC1
HTTP library with thread-safe connection pooling, file post, and more.
Library home page: https://files.pythonhosted.org/packages/e6/60/247f23a7121ae632d62811ba7f273d0e58972d75e58a94d329d51550a47d/urllib3-1.25.3-py2.py3-none-any.whl
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/python/python3-requirements.txt
Path to vulnerable library: test-samples/samples/testing-frameworks/appium/client-side/python/python3-requirements.txt,test-samples/samples/testing-frameworks/appium/client-side/python/python3-requirements.txt,test-samples/samples/testing-frameworks/desktop-browsers/server-side/python/requirements.txt,test-samples/samples/testing-frameworks/desktop-browsers/server-side/python-simple/requirements.txt,test-samples/samples/testing-frameworks/desktop-browsers/server-side/python-simple/requirements.txt,test-samples/samples/tools/azure-pipelines-extension/requirements.txt,test-samples/samples/tools/azure-pipelines-extension/requirements.txt,test-samples/samples/testing-frameworks/desktop-browsers/server-side/python/requirements.txt
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
The _encode_invalid_chars function in util/url.py in the urllib3 library 1.25.2 through 1.25.7 for Python allows a denial of service (CPU consumption) because of an inefficient algorithm. The percent_encodings array contains all matches of percent encodings. It is not deduplicated. For a URL of length N, the size of percent_encodings may be up to O(N). The next step (normalize existing percent-encoded bytes) also takes up to O(N) for each step, so the total time is O(N^2). If percent_encodings were deduplicated, the time to compute _encode_invalid_chars would be O(kN), where k is at most 484 ((10+6*2)^2).
Publish Date: 2020-03-06
URL: CVE-2020-7212
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-7212
Release Date: 2020-03-06
Fix Resolution: 1.25.8
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to net.sf.ehcache.hibernate.EhcacheJtaTransactionManagerLookup.
Publish Date: 2019-10-07
URL: CVE-2019-17267
Base Score Metrics:
Type: Upgrade version
Origin: FasterXML/jackson-databind#2460
Release Date: 2019-10-07
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10
Apache Commons BeanUtils provides an easy-to-use but flexible wrapper around reflection and introspection.
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.9.2/commons-beanutils-1.9.2.jar,/home/wss-scanner/.m2/repository/commons-beanutils/commons-beanutils/1.9.2/commons-beanutils-1.9.2.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
Apache Commons BeanUtils, as distributed in lib/commons-beanutils-1.8.0.jar in Apache Struts 1.x through 1.3.10 and in other products requiring commons-beanutils through 1.9.2, does not suppress the class property, which allows remote attackers to "manipulate" the ClassLoader and execute arbitrary code via the class parameter, as demonstrated by the passing of this parameter to the getClass method of the ActionForm object in Struts 1.
Publish Date: 2014-04-30
URL: CVE-2014-0114
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0114
Release Date: 2014-04-30
Fix Resolution: commons-beanutils:commons-beanutils:1.9.4;org.apache.struts:struts2-core:2.0.5
I'm trying to select a device with a minimum memory requirement however the memory info doesn't appear to be accessible via the API?
{"id"=>118,
"creditsPrice"=>1,
"displayName"=>"HTC Desire A8181",
"frame100Url"=>"https://cloud.testdroid.com/resources/images/devices/htc-desire-h100.png",
"frame160Url"=>"https://cloud.testdroid.com/resources/images/devices/htc-desire-h160.png",
"frame400Url"=>"https://cloud.testdroid.com/resources/images/devices/htc-desire-h400.png",
"frame80Url"=>"https://cloud.testdroid.com/resources/images/devices/htc-desire-h80.png",
"frameExtraWidth"=>nil,
"imageHeight"=>279,
"imageLeft"=>41,
"imagePrefix"=>"htc-desire",
"imageTop"=>43,
"imageWidth"=>168,
"locked"=>false,
"online"=>true,
"osType"=>"ANDROID",
"softwareVersion"=>{"id"=>7, "apiLevel"=>8, "releaseVersion"=>"2.2.2"},
"vncSupported"=>false,
"aroSupported"=>false}Failed to perform gesture. java.lang.SecurityException: Injecting to another application requires INJECT_EVENTS permission (RuntimeError) I am getting error when i write Then I press view with id "button1" in my test case in android 5.1 and 4.3
Hi,
For running desktop based application on bitbar for windows what should be the contents of run-tests.ps1? And how to run it?
I tried running akaze_match through appium on aws device farm and i got the following error:
lib/linux/akaze/akaze_match: error while loading shared libraries: libopencv_calib3d.so.2.4: cannot open shared object file: No such file or directory
Do you know what is causing it?
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.apache.commons.jelly.impl.Embedded (aka commons-jelly).
Publish Date: 2020-04-07
URL: CVE-2020-11620
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11620
Release Date: 2020-04-07
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
FasterXML jackson-databind through 2.8.11 and 2.9.x through 2.9.3 allows unauthenticated remote code execution because of an incomplete fix for the CVE-2017-7525 and CVE-2017-17485 deserialization flaws. This is exploitable via two different gadgets that bypass a blacklist.
Publish Date: 2018-01-22
URL: CVE-2018-5968
Base Score Metrics:
Type: Upgrade version
Origin: http://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-5968
Release Date: 2018-01-22
Fix Resolution: 2.8.11.1, 2.9.4
Hello,
I am looking for automation of Native Android App using webdriver.io using Appium.
Could you please provide some examples or samples?
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
FasterXML jackson-databind 2.x before 2.9.10.4 mishandles the interaction between serialization gadgets and typing, related to org.springframework.aop.config.MethodLocatingFactoryBean (aka spring-aop).
Publish Date: 2020-04-07
URL: CVE-2020-11619
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2020-11619
Release Date: 2020-04-07
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.9.10.4
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x through 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has JDOM 1.x or 2.x jar in the classpath, an attacker can send a specifically crafted JSON message that allows them to read arbitrary local files on the server.
Publish Date: 2019-06-19
URL: CVE-2019-12814
Base Score Metrics:
Type: Upgrade version
Origin: FasterXML/jackson-databind#2341
Release Date: 2019-06-19
Fix Resolution: 2.7.9.6, 2.8.11.4, 2.9.9.1, 2.10.0
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Oracle JDBC jar in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.
Publish Date: 2019-03-21
URL: CVE-2018-12023
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022
Release Date: 2019-03-21
Fix Resolution: 2.7.9.4, 2.8.11.2, 2.9.6
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
An issue was discovered in FasterXML jackson-databind prior to 2.7.9.4, 2.8.11.2, and 2.9.6. When Default Typing is enabled (either globally or for a specific property), the service has the Jodd-db jar (for database access for the Jodd framework) in the classpath, and an attacker can provide an LDAP service to access, it is possible to make the service execute a malicious payload.
Publish Date: 2019-03-21
URL: CVE-2018-12022
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-12022
Release Date: 2019-03-21
Fix Resolution: 2.7.9.4, 2.8.11.2, 2.9.6
A javascript text diff implementation.
Library home page: https://registry.npmjs.org/diff/-/diff-1.0.7.tgz
Path to dependency file: test-samples/samples/testing-frameworks/detox/react-native/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/detox/react-native/node_modules/mocha-jenkins-reporter/node_modules/diff/package.json
Dependency Hierarchy:
A javascript text diff implementation.
Library home page: https://registry.npmjs.org/diff/-/diff-3.2.0.tgz
Path to dependency file: test-samples/samples/testing-frameworks/detox/react-native/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/detox/react-native/node_modules/mocha-jenkins-reporter/node_modules/mocha/node_modules/diff/package.json
Dependency Hierarchy:
A javascript text diff implementation.
Library home page: https://registry.npmjs.org/diff/-/diff-1.4.0.tgz
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/node_modules/diff/package.json
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A vulnerability was found in diff before v3.5.0, the affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS) attacks.
Publish Date: 2018-03-05
URL: WS-2018-0590
Type: Upgrade version
Origin: kpdecker/jsdiff@2aec429
Release Date: 2019-06-11
Fix Resolution: 3.5.0
Please update device_finder.py to:
return device['displayName'].encode("ascii")As unicode is causing some troubles in testdroid_**.py scripts
The Netty project is an effort to provide an asynchronous event-driven network application framework and tools for rapid development of maintainable high performance and high scalability protocol servers and clients. In other words, Netty is a NIO client server framework which enables quick and easy development of network applications such as protocol servers and clients. It greatly simplifies and streamlines network programming such as TCP and UDP socket server.
Library home page: http://netty.io/
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/java/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/io/netty/netty/3.5.7.Final/netty-3.5.7.Final.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
WebSocket08FrameDecoder in Netty 3.6.x before 3.6.9, 3.7.x before 3.7.1, 3.8.x before 3.8.2, 3.9.x before 3.9.1, and 4.0.x before 4.0.19 allows remote attackers to cause a denial of service (memory consumption) via a TextWebSocketFrame followed by a long stream of ContinuationWebSocketFrames.
Publish Date: 2014-05-06
URL: CVE-2014-0193
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2014-0193
Release Date: 2014-05-06
Fix Resolution: io.netty:netty-all:4.0.19.Final,io.netty:netty-codec-http:4.0.19.Final,io.netty:netty:3.6.9.Final,io.netty:netty:3.7.1.Final,io.netty:netty:3.8.2.Final,io.netty:netty:3.9.1.Final
small debugging utility
Library home page: https://registry.npmjs.org/debug/-/debug-2.6.8.tgz
Path to dependency file: test-samples/samples/testing-frameworks/detox/react-native/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/detox/react-native/node_modules/mocha-jenkins-reporter/node_modules/debug/package.json
Dependency Hierarchy:
small debugging utility
Library home page: https://registry.npmjs.org/debug/-/debug-2.2.0.tgz
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/node_modules/debug/package.json
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
The debug module is vulnerable to regular expression denial of service when untrusted user input is passed into the o formatter. It takes around 50k characters to block for 2 seconds making this a low severity issue.
Publish Date: 2018-06-07
URL: CVE-2017-16137
Base Score Metrics:
Type: Upgrade version
Origin: https://nvd.nist.gov/view/vuln/detail?vulnId=CVE-2017-16137
Release Date: 2018-06-07
Fix Resolution: 2.6.9
Tiny ms conversion utility
Library home page: https://registry.npmjs.org/ms/-/ms-0.7.1.tgz
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/node_modules/ms/package.json
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
Affected versions of this package are vulnerable to Regular Expression Denial of Service (ReDoS).
Publish Date: 2017-04-12
URL: WS-2017-0247
Type: Upgrade version
Origin: vercel/ms#89
Release Date: 2017-04-12
Fix Resolution: 2.1.1
What is the alternative for Mode enum, in the new api?
Can you point me to the latest documentation?
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.0.0 through 2.9.10. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the apache-log4j-extra (version 1.2.x) jar in the classpath, and an attacker can provide a JNDI service to access, it is possible to make the service execute a malicious payload.
Publish Date: 2019-10-12
URL: CVE-2019-17531
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-17531
Release Date: 2019-10-12
Fix Resolution: 2.10
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9.2. This occurs when Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint and the service has the logback jar in the classpath.
Publish Date: 2019-07-30
URL: CVE-2019-14439
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14439
Release Date: 2019-07-30
Fix Resolution: 2.9.9.2
It'd be nice to have a device_finder.rb based on the same python class. My testdroid tests often error with the all devices are busy at the moment. Please try again later
I'd rather have them run on an available device than not run at all.
Hello, I have finished my script by referring to bitbar_android.py and run-test.py. When I run Python my run-test.py in terminal of pycharm, the following error appears
raise MaxRetryError(_pool, url, error or ResponseError(cause))
urllib3.exceptions.MaxRetryError: HTTPSConnectionPool(host='appium.bitbar.com', port=443): Max retries exceeded with url: /wd/hub:443/wd/hub/session (Caused by SSLError(SSLError("bad handshake: Error([('SSL routines', 'tls_process_server_certificate', 'certificate verify failed')])")))
I don't know how to run my script on bitbar. I can't find any useful information in bitbar's documents. It seems very complicated. I'm not sure if I need to upload the script to bitbar
Core Jackson abstractions, basic JSON streaming API implementation
Library home page: https://github.com/FasterXML/jackson-core
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-core/2.6.0/jackson-core-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
In Jackson Core before version 2.8.6 if the REST endpoint consumes POST requests with JSON or XML data and data are invalid, the first unrecognized token is printed to server.log. If the first token is word of length 10MB, the whole word is printed. This is potentially dangerous and can be used to attack the server by filling the disk with logs.
Publish Date: 2018-06-24
URL: WS-2018-0124
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=WS-2018-0124
Release Date: 2018-01-24
Fix Resolution: 2.8.6
The tests are failing everytime because of this!
I uploaded zip file, i uploaded apk, i checked .sh file too!
devicelog.log
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind before 2.9.10. It is related to com.zaxxer.hikari.HikariConfig.
Publish Date: 2019-09-15
URL: CVE-2019-14540
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-14540
Release Date: 2019-09-15
Fix Resolution: com.fasterxml.jackson.core:jackson-databind:2.8.11.5,2.9.10,2.10.0.pr3,2.11.0.rc1
Hello,
When I run your example (https://github.com/bitbar/testdroid-samples/tree/master/appium/sample-scripts/java) I get an exception. I have to do something in my account before the run the tests?
Capabilities:Capabilities [{app=bn.ereader, testdroid_device=Asus Google Nexus 7 (2013) ME571KL, testdroid_testrun=TestRun 1, testdroid_username=[email protected], platformVersion=4.4, testdroid_target=Android, platformName=Android, deviceName=Android Phone,
testdroid_project=BnEreader, app-package=bn.ereader, device=android, testdroid_app=384ca4f9-f8f5-478b-9947-bfe0bcfae83b/release.apk, app-activity=com.app.settings.SettingsActivity, testdroid_description=BnEreader international tests, te
stdroid_password=InterCore2}]
Tests run: 2, Failures: 0, Errors: 2, Skipped: 0, Time elapsed: 48.348 sec <<< FAILURE!
bn.ereader.international.SampleAppiumTest Time elapsed: 48.346 sec <<< ERROR!
java.lang.NoClassDefFoundError: org/apache/http/conn/scheme/SchemeSocketFactory
at java.net.URLClassLoader$1.run(URLClassLoader.java:366)
at java.net.URLClassLoader$1.run(URLClassLoader.java:355)
at java.security.AccessController.doPrivileged(Native Method)
at java.net.URLClassLoader.findClass(URLClassLoader.java:354)
at java.lang.ClassLoader.loadClass(ClassLoader.java:425)
at sun.misc.Launcher$AppClassLoader.loadClass(Launcher.java:308)
at java.lang.ClassLoader.loadClass(ClassLoader.java:358)
at org.openqa.selenium.remote.HttpCommandExecutor.(HttpCommandExecutor.java:100)
at org.openqa.selenium.remote.HttpCommandExecutor.(HttpCommandExecutor.java:81)
at org.openqa.selenium.remote.RemoteWebDriver.(RemoteWebDriver.java:153)
at io.appium.java_client.AppiumDriver.(AppiumDriver.java:41)
at bn.ereader.international.SampleAppiumTest.setUp(SampleAppiumTest.java:71)
bn.ereader.international.SampleAppiumTest Time elapsed: 48.348 sec <<< ERROR!
java.lang.NullPointerException: null
at bn.ereader.international.SampleAppiumTest.tearDown(SampleAppiumTest.java:76)
Results :
Tests in error:
SampleAppiumTest.setUp:71 ╗ NoClassDefFound org/apache/http/conn/scheme/Scheme...
SampleAppiumTest.tearDown:76 NullPointer
[ERROR] Failed to execute goal org.apache.maven.plugins:maven-surefire-plugin:2.14.1:test (default-test) on project SampleAppiumJava: There are test failures.
[ERROR]
[ERROR] Please refer to D:\sf.n.ivanov\encore\international\BnEreaderI18n\target\surefire-reports for the individual test results.
[ERROR] -> [Help 1]
org.apache.maven.lifecycle.LifecycleExecutionException: Failed to execute goal org.apache.maven.plugins:maven-surefire-plugin:2.14.1:test (default-test) on project SampleAppiumJava: There are test failures.
Please refer to D:\sf.n.ivanov\encore\international\BnEreaderI18n\target\surefire-reports for the individual test results.
at org.apache.maven.lifecycle.internal.MojoExecutor.execute(MojoExecutor.java:212)
at org.apache.maven.lifecycle.internal.MojoExecutor.execute(MojoExecutor.java:153)
at org.apache.maven.lifecycle.internal.MojoExecutor.execute(MojoExecutor.java:145)
at org.apache.maven.lifecycle.internal.LifecycleModuleBuilder.buildProject(LifecycleModuleBuilder.java:84)
at org.apache.maven.lifecycle.internal.LifecycleModuleBuilder.buildProject(LifecycleModuleBuilder.java:59)
at org.apache.maven.lifecycle.internal.LifecycleStarter.singleThreadedBuild(LifecycleStarter.java:183)
at org.apache.maven.lifecycle.internal.LifecycleStarter.execute(LifecycleStarter.java:161)
at org.apache.maven.DefaultMaven.doExecute(DefaultMaven.java:317)
at org.apache.maven.DefaultMaven.execute(DefaultMaven.java:152)
at org.apache.maven.cli.MavenCli.execute(MavenCli.java:555)
at org.apache.maven.cli.MavenCli.doMain(MavenCli.java:214)
at org.apache.maven.cli.MavenCli.main(MavenCli.java:158)
at sun.reflect.NativeMethodAccessorImpl.invoke0(Native Method)
at sun.reflect.NativeMethodAccessorImpl.invoke(NativeMethodAccessorImpl.java:57)
at sun.reflect.DelegatingMethodAccessorImpl.invoke(DelegatingMethodAccessorImpl.java:43)
at java.lang.reflect.Method.invoke(Method.java:606)
at org.codehaus.plexus.classworlds.launcher.Launcher.launchEnhanced(Launcher.java:289)
at org.codehaus.plexus.classworlds.launcher.Launcher.launch(Launcher.java:229)
at org.codehaus.plexus.classworlds.launcher.Launcher.mainWithExitCode(Launcher.java:415)
at org.codehaus.plexus.classworlds.launcher.Launcher.main(Launcher.java:356)
Caused by: org.apache.maven.plugin.MojoFailureException: There are test failures.
Please refer to D:\sf.n.ivanov\encore\international\BnEreaderI18n\target\surefire-reports for the individual test results.
at org.apache.maven.plugin.surefire.SurefireHelper.reportExecution(SurefireHelper.java:82)
at org.apache.maven.plugin.surefire.SurefirePlugin.handleSummary(SurefirePlugin.java:169)
at org.apache.maven.plugin.surefire.AbstractSurefireMojo.executeAfterPreconditionsChecked(AbstractSurefireMojo.java:733)
at org.apache.maven.plugin.surefire.AbstractSurefireMojo.execute(AbstractSurefireMojo.java:631)
at org.apache.maven.plugin.DefaultBuildPluginManager.executeMojo(DefaultBuildPluginManager.java:106)
at org.apache.maven.lifecycle.internal.MojoExecutor.execute(MojoExecutor.java:208)
Thanks
A utility library delivering consistency, customization, performance, and extras.
Library home page: https://registry.npmjs.org/lodash/-/lodash-1.0.2.tgz
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/node_modules/lodash/package.json
Dependency Hierarchy:
The modern build of lodash’s `_.template` as a module.
Library home page: https://registry.npmjs.org/lodash.template/-/lodash.template-3.6.2.tgz
Path to dependency file: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/appium/client-side/javascript/nightwatch_web_example/node_modules/lodash.template/package.json
Dependency Hierarchy:
The modern build of lodash modular utilities.
Library home page: https://registry.npmjs.org/lodash/-/lodash-3.10.1.tgz
Path to dependency file: test-samples/samples/testing-frameworks/detox/react-native/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/detox/react-native/node_modules/xmlbuilder/node_modules/lodash/package.json
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
Versions of lodash lower than 4.17.12 are vulnerable to Prototype Pollution. The function defaultsDeep could be tricked into adding or modifying properties of Object.prototype using a constructor payload.
Publish Date: 2019-07-26
URL: CVE-2019-10744
Base Score Metrics:
Type: Upgrade version
Origin: GHSA-jf85-cpcp-j695
Release Date: 2019-07-08
Fix Resolution: lodash-4.17.12, lodash-amd-4.17.12, lodash-es-4.17.12, lodash.defaultsdeep-4.6.1, lodash.merge- 4.6.2, lodash.mergewith-4.6.2, lodash.template-4.5.0
Hi,
I have tested my react-native project which has e2e test cases written using detox e2e library. My test case fails at testdroid when I am trying to save the data locally and stops all subsequent test cases from being tested. I have tested the app locally and it got passed, but, It is unable to get passed on the testdroid.
Is bitbar.com team supporting local storage/device storage on testdroid.
An XML builder for node.js
Library home page: https://registry.npmjs.org/xmlbuilder/-/xmlbuilder-4.0.0.tgz
Path to dependency file: test-samples/samples/testing-frameworks/detox/react-native/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/detox/react-native/node_modules/xmlbuilder/package.json
Dependency Hierarchy:
An XML builder for node.js
Library home page: https://registry.npmjs.org/xmlbuilder/-/xmlbuilder-8.2.2.tgz
Path to dependency file: test-samples/samples/testing-frameworks/detox/react-native/package.json
Path to vulnerable library: test-samples/samples/testing-frameworks/detox/react-native/node_modules/simple-plist/node_modules/xmlbuilder/package.json
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
The package xmlbuilder-js before 9.0.5 is vulnerable to denial of service due to a regular expression issue.
Publish Date: 2018-02-08
URL: WS-2018-0625
Base Score Metrics:
Type: Upgrade version
Origin: oozcitak/xmlbuilder-js@bbf929a
Release Date: 2020-03-23
Fix Resolution: 9.0.5
General data-binding functionality for Jackson: works on core streaming API
Library home page: http://github.com/FasterXML/jackson
Path to dependency file: test-samples/samples/testing-frameworks/appium/server-side/image-recognition/pom.xml
Path to vulnerable library: /home/wss-scanner/.m2/repository/com/fasterxml/jackson/core/jackson-databind/2.6.0/jackson-databind-2.6.0.jar
Dependency Hierarchy:
Found in HEAD commit: 12af4f854b64888df6e4492ecc94e141388e939a
Found in base branch: master
A Polymorphic Typing issue was discovered in FasterXML jackson-databind 2.x before 2.9.9. When Default Typing is enabled (either globally or for a specific property) for an externally exposed JSON endpoint, the service has the mysql-connector-java jar (8.0.14 or earlier) in the classpath, and an attacker can host a crafted MySQL server reachable by the victim, an attacker can send a crafted JSON message that allows them to read arbitrary local files on the server. This occurs because of missing com.mysql.cj.jdbc.admin.MiniAdmin validation.
Publish Date: 2019-05-17
URL: CVE-2019-12086
Base Score Metrics:
Type: Upgrade version
Origin: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2019-12086
Release Date: 2019-05-17
Fix Resolution: 2.9.9
A declarative, efficient, and flexible JavaScript library for building user interfaces.
🖖 Vue.js is a progressive, incrementally-adoptable JavaScript framework for building UI on the web.
TypeScript is a superset of JavaScript that compiles to clean JavaScript output.
An Open Source Machine Learning Framework for Everyone
The Web framework for perfectionists with deadlines.
A PHP framework for web artisans
Bring data to life with SVG, Canvas and HTML. 📊📈🎉
JavaScript (JS) is a lightweight interpreted programming language with first-class functions.
Some thing interesting about web. New door for the world.
A server is a program made to process requests and deliver data to clients.
Machine learning is a way of modeling and interpreting data that allows a piece of software to respond intelligently.
Some thing interesting about visualization, use data art
Some thing interesting about game, make everyone happy.
We are working to build community through open source technology. NB: members must have two-factor auth.
Open source projects and samples from Microsoft.
Google ❤️ Open Source for everyone.
Alibaba Open Source for everyone
Data-Driven Documents codes.
China tencent open source team.